Enlarge / The security of Facebook's popular messaging app leaves several rather important devils in its details.
Yesterday, independent newsroom ProPublica published a detailed piece examining the popular WhatsApp messaging platform's privacy claims. The service famously offers "end-to-end encryption," which most users interpret as meaning that Facebook, WhatsApp's owner since 2014, can neither read messages itself nor forward them to law enforcement.
This claim is contradicted by the simple fact that Facebook employs about 1,000 WhatsApp moderators whose entire job is—you guessed it—reviewing WhatsApp messages that have been flagged as "improper."
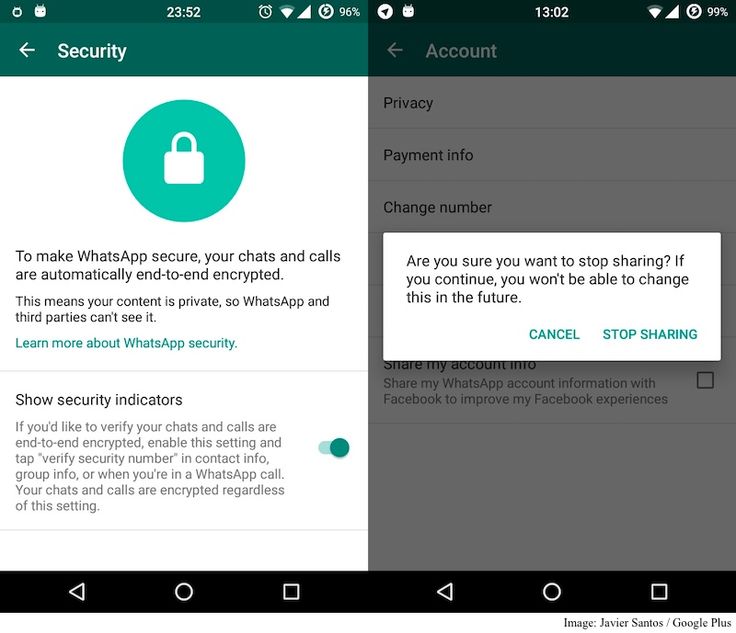
Enlarge / This snippet from WhatsApp's security and privacy page seems easy to misinterpret.
Jim Salter
The loophole in WhatsApp's end-to-end encryption is simple: The recipient of any WhatsApp message can flag it. Once flagged, the message is copied on the recipient's device and sent as a separate message to Facebook for review.
Messages are typically flagged—and reviewed—for the same reasons they would be on Facebook itself, including claims of fraud, spam, child porn, and other illegal activities. When a message recipient flags a WhatsApp message for review, that message is batched with the four most recent prior messages in that thread and then sent on to WhatsApp's review system as attachments to a ticket.
Although nothing indicates that Facebook currently collects user messages without manual intervention by the recipient, it's worth pointing out that there is no technical reason it could not do so. The security of "end-to-end" encryption depends on the endpoints themselves—and in the case of a mobile messaging application, that includes the application and its users.
AdvertisementAn "end-to-end" encrypted messaging platform could choose to, for example, perform automated AI-based content scanning of all messages on a device, then forward automatically flagged messages to the platform's cloud for further action.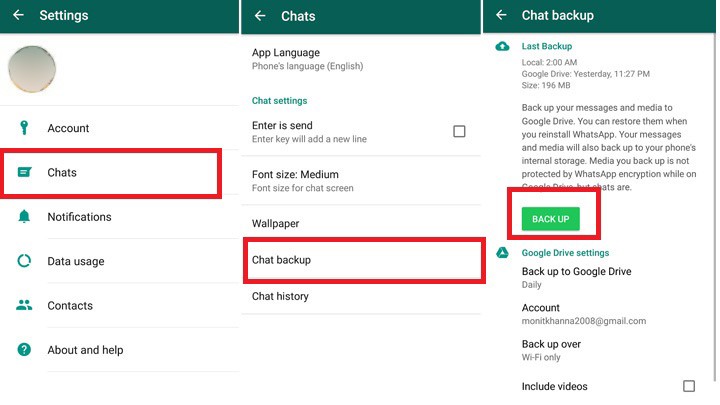 Ultimately, privacy-focused users must rely on policies and platform trust as heavily as they do on technological bullet points.
Ultimately, privacy-focused users must rely on policies and platform trust as heavily as they do on technological bullet points.
Once a review ticket arrives in WhatsApp's system, it is fed automatically into a "reactive" queue for human contract workers to assess. AI algorithms also feed the ticket into "proactive" queues that process unencrypted metadata—including names and profile images of the user's groups, phone number, device fingerprinting, related Facebook and Instagram accounts, and more.
Human WhatsApp reviewers process both types of queue—reactive and proactive—for reported and/or suspected policy violations. The reviewers have only three options for a ticket—ignore it, place the user account on "watch," or ban the user account entirely. (According to ProPublica, Facebook uses the limited set of actions as justification for saying that reviewers do not "moderate content" on the platform.)
Although WhatsApp's moderators—pardon us, reviewers—have fewer options than their counterparts at Facebook or Instagram do, they face similar challenges and have similar hindrances. Accenture, the company that Facebook contracts with for moderation and review, hires workers who speak a variety of languages—but not all languages. When messages arrive in a language moderators are not conversant in, they must rely on Facebook's automatic language-translation tools.
Accenture, the company that Facebook contracts with for moderation and review, hires workers who speak a variety of languages—but not all languages. When messages arrive in a language moderators are not conversant in, they must rely on Facebook's automatic language-translation tools.
"In the three years I've been there, it's always been horrible," one moderator told ProPublica. Facebook's translation tool offers little to no guidance on either slang or local context, which is no surprise given that the tool frequently has difficulty even identifying the source language. A shaving company selling straight razors may be misflagged for "selling weapons," while a bra manufacturer could get knocked as a "sexually oriented business."
AdvertisementWhatsApp's moderation standards can be as confusing as its automated translation tools—for example, decisions about child pornography may require comparing hip bones and pubic hair on a naked person to a medical index chart, or decisions about political violence might require guessing whether an apparently severed head in a video is real or fake.
Unsurprisingly, some WhatsApp users also use the flagging system itself to attack other users. One moderator told ProPublica that "we had a couple of months where AI was banning groups left and right" because users in Brazil and Mexico would change the name of a messaging group to something problematic and then report the message. "At the worst of it," recalled the moderator, "we were probably getting tens of thousands of those. They figured out some words that the algorithm did not like."
Although WhatsApp's "end-to-end" encryption of message contents can only be subverted by the sender or recipient devices themselves, a wealth of metadata associated with those messages is visible to Facebook—and to law enforcement authorities or others that Facebook decides to share it with—with no such caveat.
ProPublica found more than a dozen instances of the Department of Justice seeking WhatsApp metadata since 2017. These requests are known as "pen register orders," terminology dating from requests for connection metadata on landline telephone accounts. ProPublica correctly points out that this is an unknown fraction of the total requests in that time period, as many such orders, and their results, are sealed by the courts.
ProPublica correctly points out that this is an unknown fraction of the total requests in that time period, as many such orders, and their results, are sealed by the courts.
Since the pen orders and their results are frequently sealed, it's also difficult to say exactly what metadata the company has turned over. Facebook refers to this data as "Prospective Message Pairs" (PMPs)—nomenclature given to ProPublica anonymously, which we were able to confirm in the announcement of a January 2020 course offered to Brazilian department of justice employees.
Although we don't know exactly what metadata is present in these PMPs, we do know it's highly valuable to law enforcement. In one particularly high-profile 2018 case, whistleblower and former Treasury Department official Natalie Edwards was convicted of leaking confidential banking reports to BuzzFeed via WhatsApp, which she incorrectly believed to be "secure."
FBI Special Agent Emily Eckstut was able to detail that Edwards exchanged "approximately 70 messages" with a BuzzFeed reporter "between 12:33 am and 12:54 am" the day after the article published; the data helped secure a conviction and six-month prison sentence for conspiracy.
Cryptographer and computer scientist Mayank Varia, a Boston University Faculty of Computing & Data Sciences associate professor, says his work can help balance privacy and human rights with online trust and safety.
Cryptography
August 10, 2022
Twitter Facebook
Cryptographers love an enigma, a problem to solve—and this one has it all. Indestructible codes, secret notes, encryption, and decryption.
Here’s the puzzle: someone wants to send a secure message online. It has to be so private, so secret, that they can deny they ever sent it.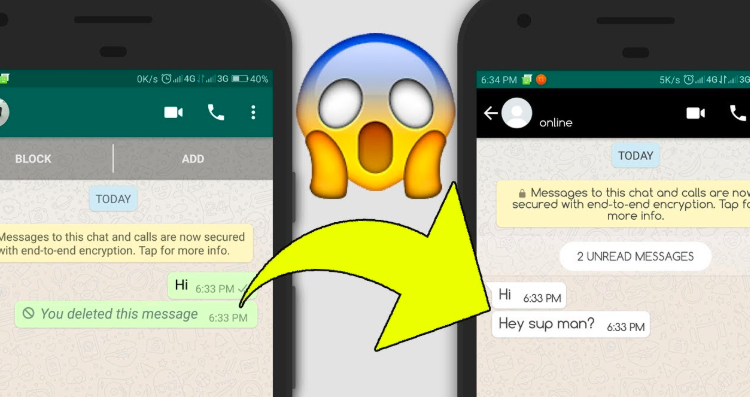 If someone leaks the message, it can never be traced back to the sender. It’s all very Mission: Impossible. But there’s a kicker: if that message peddles abuse or misinformation, maybe threatens violence, then anonymity may need to go out the window—the sender needs to be held to account.
If someone leaks the message, it can never be traced back to the sender. It’s all very Mission: Impossible. But there’s a kicker: if that message peddles abuse or misinformation, maybe threatens violence, then anonymity may need to go out the window—the sender needs to be held to account.
And that’s the challenge: is there a way to allow people to send confidential, secure, untraceable messages, but still track any menacing ones?
Mayank Varia might have cracked the conundrum. A cryptographer and computer scientist, Varia is an expert on the societal impact of algorithms and programs, developing systems that balance privacy and security with transparency and social justice. Working with a team of Boston University computer scientists, he’s designed a program called Hecate—fittingly named after the ancient Greek goddess of magic and spells—that can be bolted onto a secure messaging app to beef up its confidentiality, while also allowing moderators to crack down on abuse. The team is presenting its findings at the 31st USENIX Security Symposium.
The team is presenting its findings at the 31st USENIX Security Symposium.
“Our goal in cryptography is to build tools and systems that allow people to get things done safely in the digital world,” says Varia, a BU Faculty of Computing & Data Sciences associate professor. “The question at play in our paper is what is the most effective way to build a mechanism for reporting abuse—the fastest, most efficient way to provide the strongest security guarantees and provide the weakest possible puncturing of that?”
It’s an approach he’s also applying beyond messaging apps, building online tools that allow local governments to track gender wage gaps—without accessing private salary data—and enable sexual assault victims to more safely report their attackers.
When two people chat in a private room, what they talk about is just between them—there’s no paper trail, no recording; the conversation lives on in memory alone.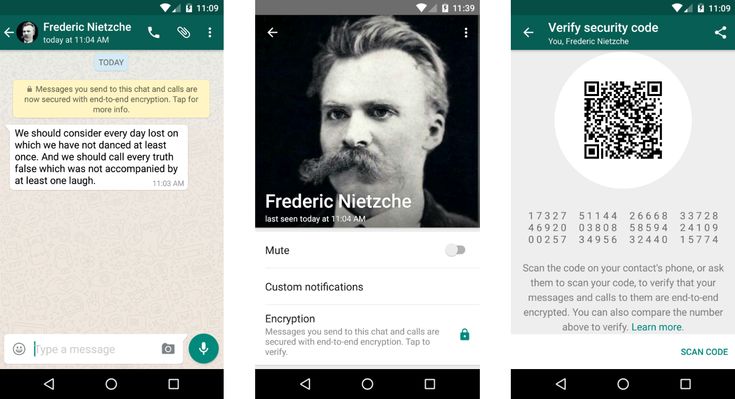 Put the same conversation online—Twitter, Facebook, email—and it’s a different story. Every word is preserved for history. Sometimes that’s good, but just as often it’s not. An activist in an authoritarian state trying to get word to a journalist or a patient seeking help for a private health issue might not want their words broadcast to the world or held in an archive.
Put the same conversation online—Twitter, Facebook, email—and it’s a different story. Every word is preserved for history. Sometimes that’s good, but just as often it’s not. An activist in an authoritarian state trying to get word to a journalist or a patient seeking help for a private health issue might not want their words broadcast to the world or held in an archive.
That’s where end-to-end encryption comes in. Popularized by apps like WhatsApp and Signal, it scrambles sent messages into an unreadable format, only decrypting them when they land on the recipient’s phone. It also ensures messages sent from one person to another can’t be traced back to the sender; just like that private in-person chat, it’s a conversation without a trail or record—everything is deniable.
“The goal of these deniable messaging systems is that even if my phone is compromised after we’ve had an encrypted messaging conversation, there are no digital breadcrumbs that will allow an external person to know for sure what we sent or even who said it,” says Varia.
Amnesty International calls encryption a human right, arguing it’s “an essential protection of [everyone’s] rights to privacy and free speech,” and especially vital for those countering corruption or challenging governments. Like much in the online world though, that privacy can be exploited or bent to more sinister ends. “There are specific times where this can be a bad thing,” says Varia. “Suppose the messages someone is sending are harassing and abusive and you want to go seek help, you want to be able to prove to the moderator what the message contents were and who said them to you.”
A study of elementary, middle, and high school students in Israel, where more than 97 percent of kids reportedly use WhatsApp, found 30 percent had been bullied on the app, while UK prosecutors have said end-to-end encryption could harm their ability to catch and stop child abusers. Extremist groups, from Islamic State to domestic terrorists, have leaned on encrypted apps like Telegram and Signal to spread their calls for violence.
The task for tech companies is finding a way to support the right to privacy with the need for accountability. Hecate offers a way to do both—it allows app users to deny they ever sent a message, but to also be reported if they say something abusive.
Developed by Varia and doctoral students Rawane Issa (GRS’22) and Nicolas Alhaddad (GRS’24), Hecate starts with the accountability side of that contradictory deniable and traceable combination. Using the program, an app’s moderator creates a unique batch of electronic signatures—or tokens—for each user. When that user sends a message, a hidden token goes along for the ride. If the recipient decides to report that message, the moderator will be able to verify the sender’s token and take action. It’s called asymmetric message franking.
The fail-safe, says Varia, the part that allows for deniability, is that the token is only useful to the moderator.
That’s the nifty part about our system: even if the moderator goes rogue, they can’t show and convince the rest of the world—they have no digital proof, no breadcrumbs they can show to anyone else.
Mayank Varia, a BU Faculty of Computing & Data Sciences associate professor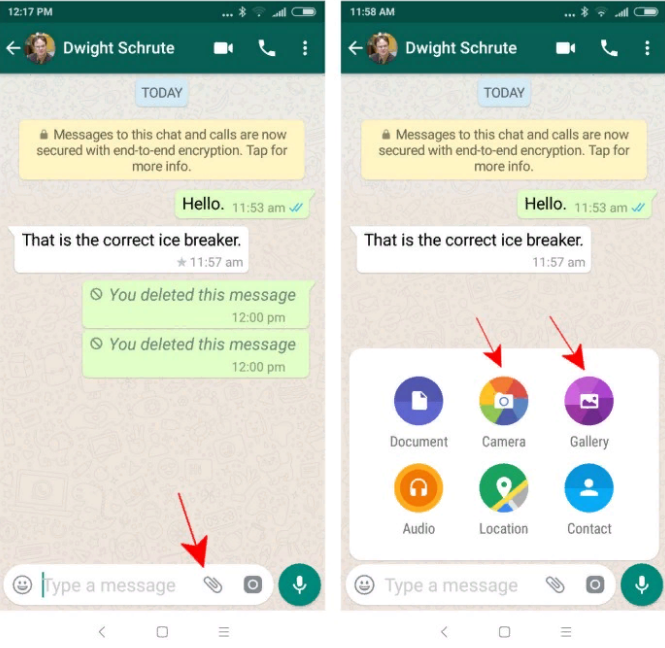
“The token is an encrypted statement that only the moderator knows how to read—it’s like they wrote a message in invisible ink to their future self,” says Varia. “The moderator is the one who builds these tokens. That’s the nifty part about our system: even if the moderator goes rogue, they can’t show and convince the rest of the world—they have no digital proof, no breadcrumbs they can show to anyone else.”
The user can maintain deniability—at least publicly.
Similar message franking systems already exist—Facebook parent Meta uses one on WhatsApp—but Varia says Hecate is faster, more secure, and futureproof in a way current programs are not.
“Hecate is the first message franking scheme that simultaneously achieves fast execution on a phone and for the moderator server, support for message forwarding, and compatibility with anonymous communication networks like Signal’s sealed sender,” says Varia. “Previous constructions achieved at most two of these three objectives.”
“Previous constructions achieved at most two of these three objectives.”
The team says Hecate could be ready for implementation on apps like Signal and WhatsApp with just a few months of custom development and testing. But despite its technological advantages, Varia suggests companies approach Hecate with caution until they’ve fully investigated its potential societal impact.
“There’s a question of, can we build this, there’s also a question of, should we build this?” says Varia. “We can try to design these tools that provide safety benefits, but there might be longer dialogues and discussions with affected communities. Are we achieving the right notion of security for, say, the journalist, the dissident, the people being harassed online?”
As head of CDS’ Hub for Civic Tech Impact, Varia is used to considering the societal and policy implications of his research. The hub’s aim is to develop software and algorithms that advance public interest, whether they help to fight misinformation or foster increased government transparency. A theme through recent projects is the creation of programs that, like Hecate, straddle the line between privacy and accountability.
A theme through recent projects is the creation of programs that, like Hecate, straddle the line between privacy and accountability.
During a recent partnership with the Boston Women’s Workforce Council, for example, BU computer scientists built a gender wage gap calculator that enables companies to share salaries with the city without letting sensitive pay data leave their servers.
“We’re designing tools that allow people—it sounds counterintuitive—to compute data that they cannot see,” says Varia, who’s a member of the federal government’s Advisory Committee on Data for Evidence Building. “Maybe I want to send you a message, but I don’t want you to read it; it’s weird, but maybe a bunch of us are sending information and we want you to be able to do some computation over it.”
That’s caught the interest of the Defense Advanced Research Projects Agency and Naval Information Warfare Center, which both funded the work that led to Hecate and have an interest in asking computer experts to crunch data without ever seeing the secrets hidden within it.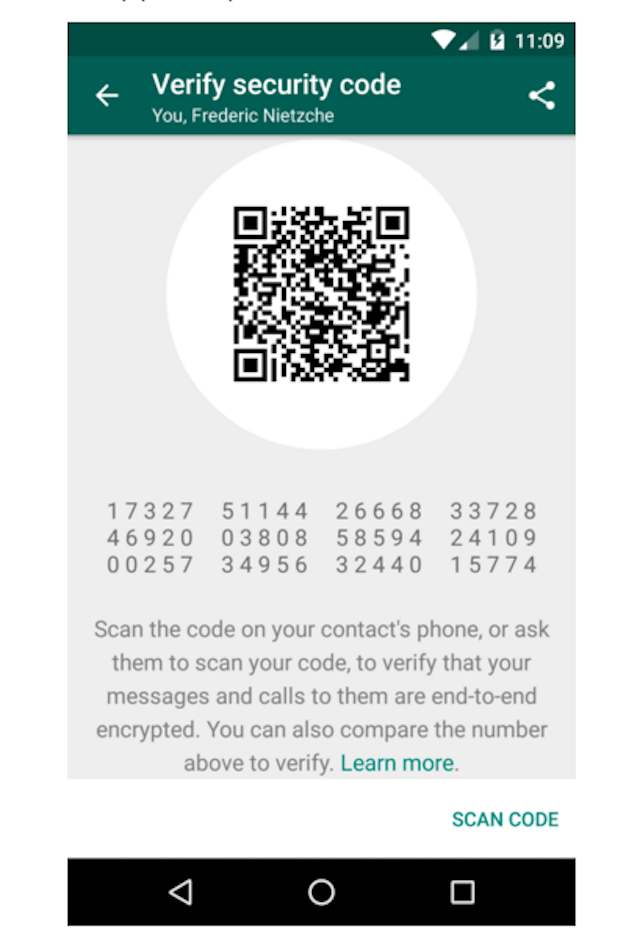
Varia’s approach to encryption could also benefit survivors of sexual abuse. He recently partnered with San Francisco–based nonprofit Callisto to develop a new secure sexual assault reporting system. Inspired by the #MeToo movement, its goal is to help assault victims who are frightened of coming forward.
“They report their instance of sexual assault into our system and that report kind of vanishes into the ether,” says Varia. “But if somebody else reports also being assaulted by the same perpetrator, then—and only then—does the system identify the existence of this match.”
That information goes to a volunteer attorney—bound by attorney-client privilege—who can then work with the victims and survivors on next steps. Just like Hecate, Varia says, it finds a balance between privacy and openness, between deniability and traceability.
“When we talk about trade-offs between privacy, digital civil liberties, and other rights, sometimes there is a natural tension,” says Varia.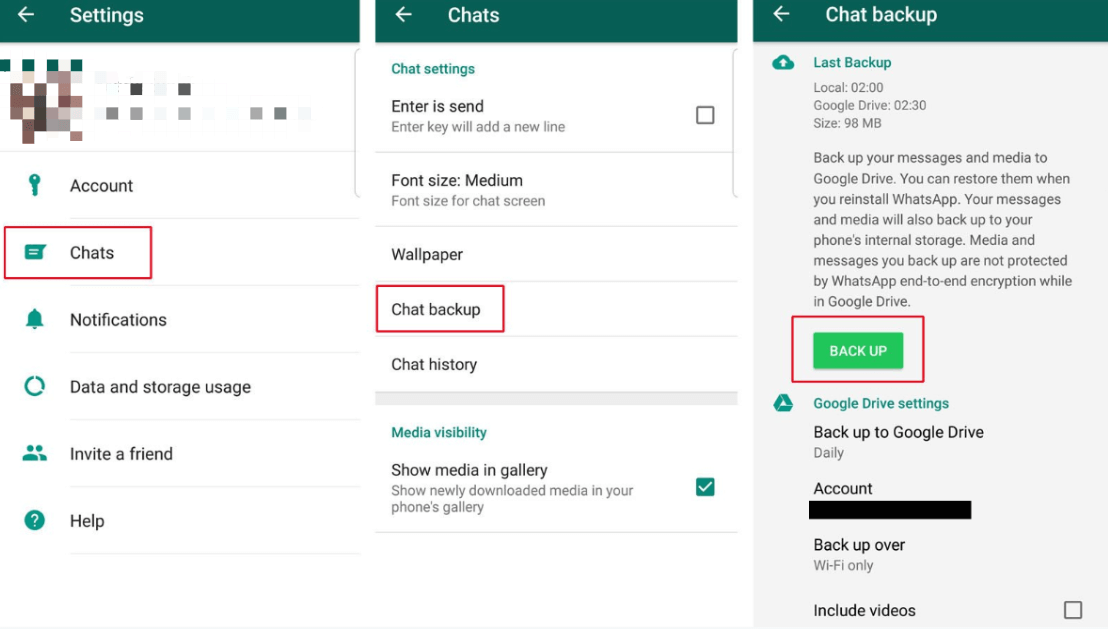 “But we can do both: we don’t have to build a system that allows for bulk surveillance, wide-scale attribution of metadata of who’s talking to who; we can provide strong personal privacy and human rights, while also providing online trust and safety, and helping people who need it.”
“But we can do both: we don’t have to build a system that allows for bulk surveillance, wide-scale attribution of metadata of who’s talking to who; we can provide strong personal privacy and human rights, while also providing online trust and safety, and helping people who need it.”
All major messaging services like WhatsApp, Facebook Messenger, Telegram, etc.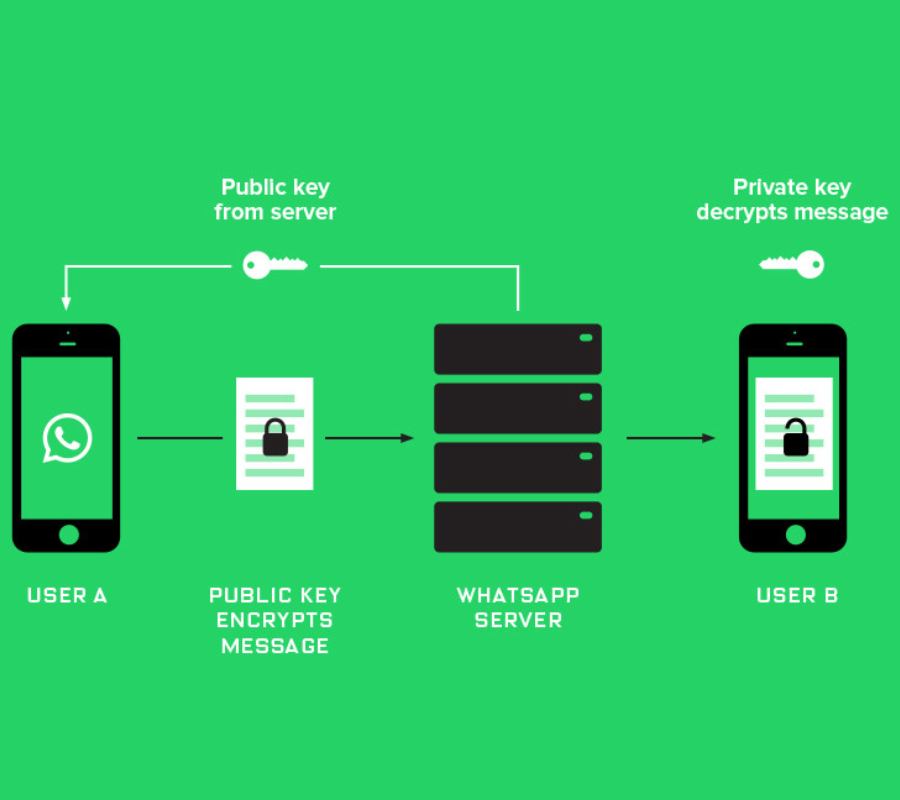 use End-to-End Encryption. It simply means that you and the other person you are communicating with can read what has been sent. No one else, including the messaging service, will be able to decrypt your message. But what if someone took their phone and read your conversations? Log into Overseas, an encryption app that provides real-time encryption. This means that even if someone takes over your WhatsApp conversation, all they see is random words.
use End-to-End Encryption. It simply means that you and the other person you are communicating with can read what has been sent. No one else, including the messaging service, will be able to decrypt your message. But what if someone took their phone and read your conversations? Log into Overseas, an encryption app that provides real-time encryption. This means that even if someone takes over your WhatsApp conversation, all they see is random words.
Oversec This is a simple application for encrypting email, text and images using open source encryption methods. The app encrypts your texts in real time and only the person using the same app can decrypt them. But the only caveat is that it is only available for Android. Sorry iPhone users.
For example, let's say you want to send a private message using WhatsApp. To do this, you need to install and set up the Oversec app on your phone as well as on the recipient's phones. Then send a regular WhatsApp message while Oversec is running in the background.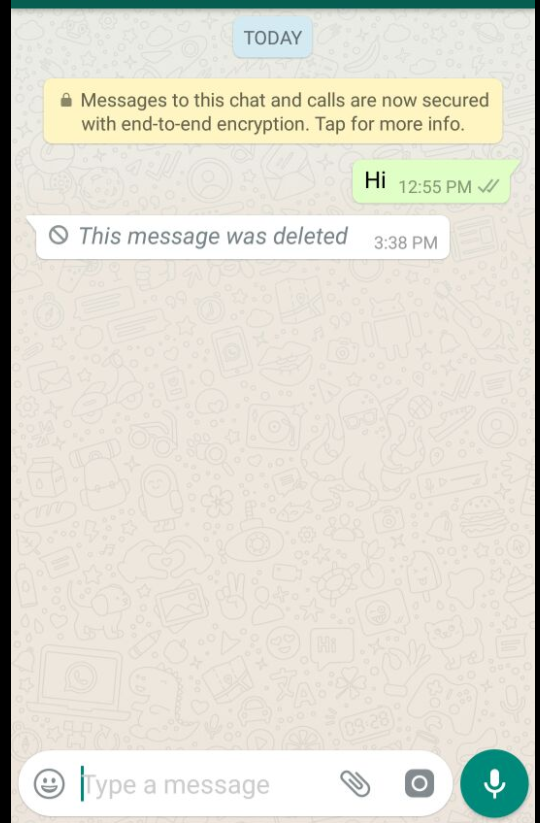 Oversec will detect and encrypt the text and return the encrypted message to the active input field. This real-time encryption happens almost instantly, and if someone reads it without the Oversec application, they will see only opaque and context-free sentences.
Oversec will detect and encrypt the text and return the encrypted message to the active input field. This real-time encryption happens almost instantly, and if someone reads it without the Oversec application, they will see only opaque and context-free sentences.
Oversec allows you to encrypt texts in real time, as well as use it to encrypt emails and even photos. It uses symmetric encryption based on ChaCha20 and Poly1305 MAC encryption with 256-bit keys. Think Twitter and Facebook encryption: Oversec encryption complies with these standards. It then encrypts the data into a more natural character set that hides the encrypted message in plain sight and makes it easier to send via WhatsApp and Instagram.
You can also use the Open PGP Keychain to encrypt your messages, but this also adds 2 KB of extra weight to your texts, which can increase data consumption. If you want to send sensitive information via WhatsApp, it is recommended to use PGP encryption. For secure conversations on WhatsApp, symmetric encryption works well.
For secure conversations on WhatsApp, symmetric encryption works well.
It is very easy to encrypt WhatsApp, Instagram with this application. You can follow the steps below to set up the app on your phone and after that you can use it to have secure conversations via WhatsApp, Instagram, Facebook Messenger, etc. It works the same for most apps.
First, install the app on your smart phone first. You can get it either from متجر Play or F-Droid. After installing an app, you must grant permissions to it before you can start using the app.
Oversec uses an accessibility service to retrieve information from an input field. To make things easier for the user, it automatically extracts the information and places it in an encrypted message. Also, displaying the decrypted message over the original encrypted message is dependent on other applications. It's not the most intuitive method, I admit, but it encrypts text instantly.
Once installed, the application will automatically take you to the accessibility page and you can activate the service manually. If for some reason you can't find the "Accessibility" section, you can search for "Accessibility" in the "Settings" and "Enable Abroad" search bar.
It also needs permission to fetch data from other applications to work properly. Grant it that permission, and once you've done that, you'll be ready to use the app. Now we will set up encryption on the device.
Make sure that Oversec is installed on all smartphones before proceeding to secure conversations. If your friend hasn't set up the correct encryption, they won't be able to read encrypted messages even with the Oversec app.
To make it easier, we are going to set up a simple symmetric key and share it with all devices. First, let's create a key on one device.
Open the Oversec application and click the "Keys" tab, then click the "+" button in the bottom left corner and select "Random Key" which is the most secure type of key.
Now give your key an alias that will help you distinguish it from other keys you create in the future. To keep things simple, let's call it "WhatsApp encrypted". Once the key has been generated, you can simply share it with your friends using the QR code.
The key on the first machine will work with multiple people and you must be sure to keep the key safe. Only share the key with people you know and trust. To install the switch on another device, open Open Overs and click the Switches button. Touch the QR code to scan the code.
You also need to make sure that the generated key is the same. Make sure the fingerprints are the same on both devices. Then press the blue button. Now the keys are configured on both devices. Now you can freely and securely connect to Oversec.
Oversec also supports simple password-based keys that, while not secure enough, can easily be shared with others.
Open the Oversec app and make sure WhatsApp is enabled, then go to WhatsApp and Oversec should show up in WhatsApp messages. To encrypt messages, press and hold the lock icon to open the settings menu.
To encrypt messages, press and hold the lock icon to open the settings menu.
We will use the key we created earlier to encrypt our messages. Click Symmetric Key and select your pre-shared key. Select it and choose an encoding. Oversec uses different encodings to encapsulate the cipher into a more natural character set. This makes your messages less suspicious. You can choose any encoding and start sending the message.
After writing a message, press the lock button to encrypt the text. A green frame should appear in the text box. After that, you can click on the "Submit" button to send the message. If another person has set the app to the same key, you will see the decrypted message.
Oversec also claims to allow you to send encrypted images via WhatsApp, but that didn't work in my testing. I've submitted feedback and maybe once the issue is resolved we'll update the steps for that as well.
Using Oversec on Instagram is similar to WhatsApp and you can follow the same steps to send private and encrypted messages on Instagram.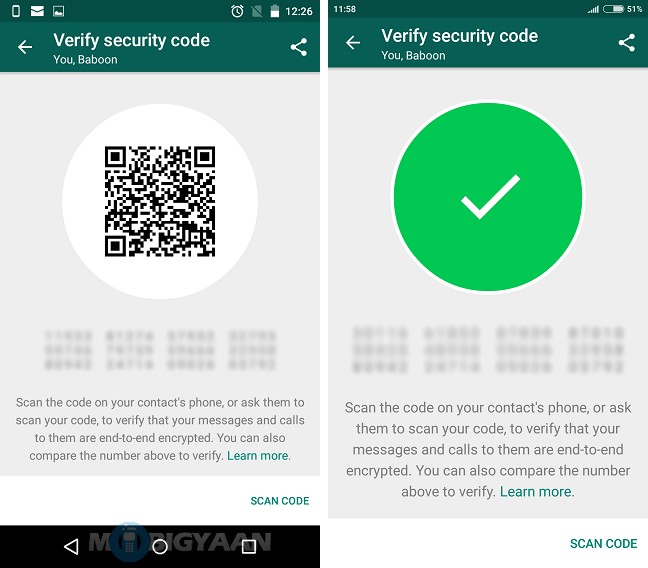
I also used Oversec to send and receive encrypted email and it still had issues with PGP encryption. The Gmail app doesn't support regular encryption, so when sending messages encrypted with Oversec, it looks like this.
Oversec is a really promising project that aims to provide real-time encryption without using the Internet. You can integrate OpenKeychain to encrypt your messages with PGP encryption. It has 20-bit ChaCha1305 and Poly256 encoders that comply with Twitter encryption standards. Your data does not leave the phone, and encryption is performed in the system. There are some bugs that I hope will be fixed in the future. The user interface is not compatible with all devices and is a bit buggy. Other than that, I don't see any reason why you wouldn't want to use the Oversec app. Try Oversec and share your experience in the comments below.
Source
May 14, 2016
Home » Security • Mobile » WhatsApp encryption - what is it, how to enable it, why and how does it work?
Contents
Not so long ago, the most popular WhatsApp messenger included a mechanism for encrypting correspondence and, in general, any data transmitted between users. One of my friends asked why this is actually necessary.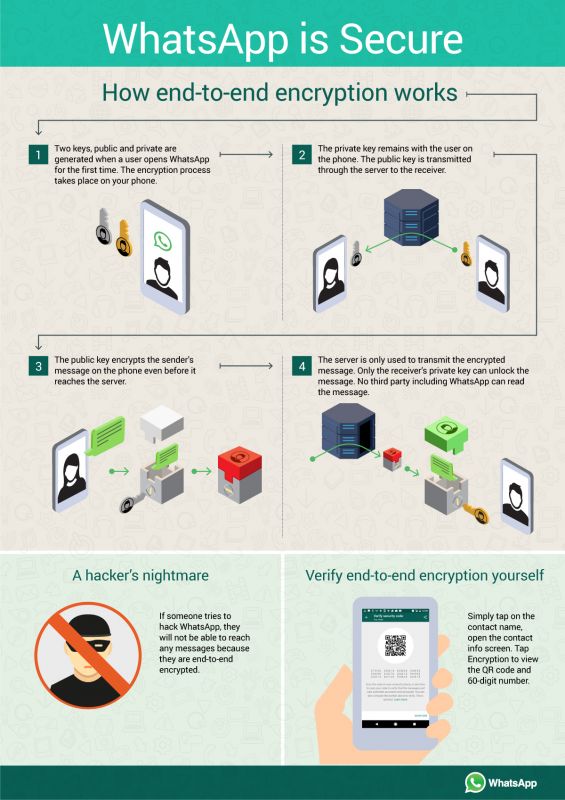 We researched the issue a little and I decided to share it with you. In fact, such encryption is a bit of a problem for intelligence agencies and governments, but in general this can be assessed positively, since for most people it is much more profitable that their conversations cannot be listened to.
We researched the issue a little and I decided to share it with you. In fact, such encryption is a bit of a problem for intelligence agencies and governments, but in general this can be assessed positively, since for most people it is much more profitable that their conversations cannot be listened to.
Namely, this is what encryption is for. This mechanism encrypts all transmitted data and even if someone can intercept it, they will not be able to read and use it. I talked a little about traffic interception in my recent consultation article on the security of transmitted data. Encryption protects us from MITM attacks, which is easy for intelligence agencies or other authorities to organize simply by contacting the provider. But if the transmitted data is encrypted - even if the provider provides access - no one can decrypt the data without having a private key - yours or the interlocutor. Whatsapp support site says:
This is a standard public key cryptographic scheme. It works like this:
It works like this:
How does Whatsapp encryption work?
WhatsApp user data encryption system (public key encryption). In order to send a message to user B, user A requests the public key for user B from the messenger server. User A then uses this public key to encrypt the message. After that, user B uses a private key, available only on his device, to decrypt the received message geektimes.ru
This means that even if the data passes through the servers of Whatsapp itself, it passes there in the same encrypted form. Accordingly, no one except the chat participants will be able to read them.
It is enabled by default, it is enough to update the version of the program to the one where the feature is already enabled.
After that, you will see such a message in the chat, where both participants have an encrypted version:
If you click on this message, an explanation will appear and a button through which you can check the encryption.