When I’m not studying videos of raccoons online (know your enemy!), I’m fielding requests from wannabe hackers all around the world because I work for Hacker Highschool. So, wannabe hackers tend to think our curriculum is there as a checklist of scriptkiddie tools that lets them DoS your online competition of Banjo Hero or creep into private Instagram accounts.
And it is. But it isn’t.
First, I recognize that hacking an Instagram password is wrong. I get it. Even if it’s their brother’s Instagram account they want to get into. Because it’s family that makes it okay, I guess. So yes, it's illegal, but being illegal doesn't make it wrong. But it’s wrong because guessing a password isn’t hacking, and not because it’s their brother. And this is why so many nascent hacker-wannabes who want to learn hacking don’t really want to learn hacking. They want to learn computer magic, and it doesn’t really work like that.
How it works is actual work. And it’s a grind sometimes. What’s strange is that so many people today can spend actual days virtually cutting virtual trees in a virtual world to get to level three tree warrior, but won’t spend an hour trying requests through Tamper Data to understand how Instagram on the web is authenticating people differently than the app. Strange because both are really not much more than pushing a cursor around a screen.
So, teaching you hacking is partly about teaching you how to set up and execute a kind of work grind. Then there’s the mindset thing too. But you know what, you need a mindset to get out of bed and go to work too, and that trumps the hacker mindset in the mornings. So, let’s leave the hacker mindset for those who already have the will to do the work grind mindset, because you won’t have one without the other.
The last part of teaching you to hack an Instagram account is that by the time I teach you what you need to know with OS, protocols, services, daemons, applications, authentication, and encryption, and what you need to do with hiding, relaying, bouncing, testing, fuzzing, tracing, trying, retrying, and learning from your frequent failures, you’ll know too much about how little you really know and how you could get caught doing it.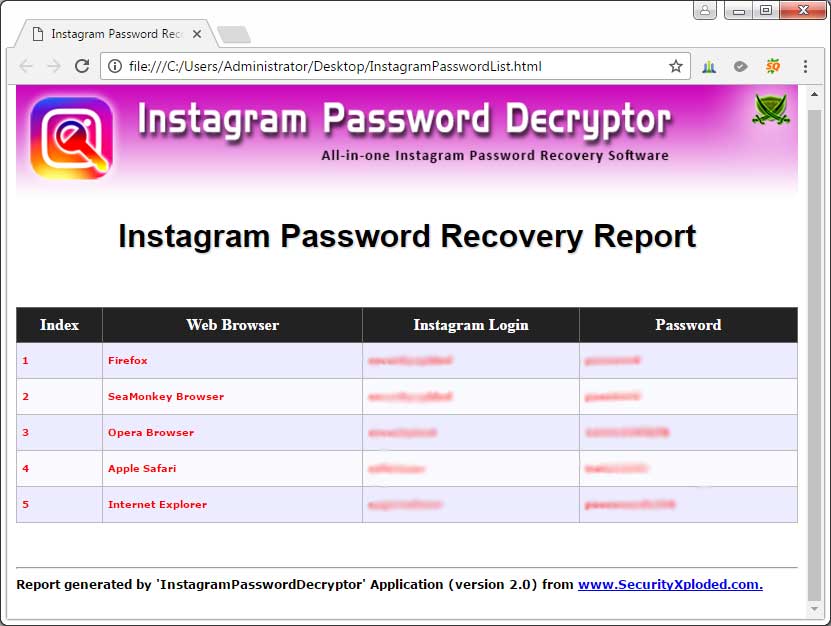 So, you probably won’t be doing anything illegal. They say a little knowledge is a dangerous thing, but when we’re talking about a skill like hacking that focuses on knowledge-gettin’ then you can expect to quickly have more than enough knowledge to see your own foolishness.
So, you probably won’t be doing anything illegal. They say a little knowledge is a dangerous thing, but when we’re talking about a skill like hacking that focuses on knowledge-gettin’ then you can expect to quickly have more than enough knowledge to see your own foolishness.
Unless you want me to just tell you to use the instacrack tool for Windows available on the ISECOM website to just put in an account name and view private account pictures. But that’s telling, not teaching, and it’s running a tool and not hacking. Also, don’t ask me how to cook if you want me to show you how to warm up a TV dinner.
But if that’s really what you want, then you never wanted to be a hacker, which means your life is about only having enough knowledge to be dangerous. Which is okay if you want to be an amateur assassin or a cashier in a natural foods store for the rest of your life. Not judging. We all have our dreams. But then you’re looking in the wrong place.
Next thing to understand: hacking isn't a tool, it's a methodology. You likely won't be able to hack an established service without considerable time spent learning its operations and interactions. Which isn’t necessarily hard. It’s actually pretty straight-forward.
You likely won't be able to hack an established service without considerable time spent learning its operations and interactions. Which isn’t necessarily hard. It’s actually pretty straight-forward.
The fact of this is that there's only two ways to steal anything: either you take it, or someone gives it to you. You need to trick Instagram to give you their credentials. Or you need to trick the person whose credentials you want to steal into giving it to you. Or you need to take it from them, or Instagram. But it's likely you won't be able to take it from Instagram. Not impossible, just not likely because they have a lot more people with a lot more experience working on securing it then you have for breaking it. Supposedly. Who knows? Maybe you’ll get lucky. People win the lottery all the time. That’s why so many people play it.
Then those two ways actually expand into four tactics that you try against both the target sender and target receiver. These four:
 ). The environment is completely under the target’s control, so it’s important to figure out how they set up their applications to live there.
). The environment is completely under the target’s control, so it’s important to figure out how they set up their applications to live there. But lose them the right way and they might give you a surprise, like access.
But lose them the right way and they might give you a surprise, like access.So there. Use those four. Now you know where your targets are and the tactics to try. That leaves you with a few options in your grind. If you need more specific examples on you how you would apply these four tactics to real-world, how would you take over your brother’s Instagram account, here's five common ones to get you started:
 Same with setting up a website that looks like Instagram for him to log into and then captures the password instead and then forwards him onto the real Instagram site so he doesn't know you took it.
Same with setting up a website that looks like Instagram for him to log into and then captures the password instead and then forwards him onto the real Instagram site so he doesn't know you took it.
Now I’d like to tell you don’t do things that have worked before because system designers learn from their mistakes and the mistakes made by others. Unfortunately, they don’t. It’s not like Engineering students are forced to take a competency exam in all the mistakes previously done in engineering. Oh, if only! I would totally take that class just for fun! But they don’t, so feel free to try things that worked in the past.
So that's it. No matter what you do, it will require more than just a tool. Because if was a tool that does some magic and then you get in, then you probably can’t afford that tool. Good magic isn’t cheap. Think about it: anyone who went through all the hard work to figure out how to do that wouldn't release a tool, as that info is way too profitable.
So, there’s no Windows-based instacrack tool either. Just kidding! I’m sure you already checked though.
Skip to main content
How To hack Someone's Instagram AccountMaat Hernandez

Published Mar 5, 2023
+ Follow
Instagram has become a vital part of our lives, and it is no surprise that people are interested in learning how to hack an Instagram account. While hacking someone's account is illegal and unethical, ethical hacking can be used to enhance security and protect against malicious attacks. Ethical hacking involves identifying vulnerabilities in a system and exploiting them to improve security. In this blog post, we will discuss how to hack someone's Instagram account.
Ethical hacking is a process of identifying security vulnerabilities in a system or network and using them to improve security. It is an authorized and legal way of identifying weaknesses in a system to enhance its security. Ethical hackers are also known as white hat hackers, and they use their skills to help organizations and businesses identify and fix security vulnerabilities. Ethical hacking is crucial in protecting personal and sensitive information from cyber-criminals.
To perform ethical hacking on an Instagram account, you need to identify the vulnerabilities in the system. Some of the common vulnerabilities include weak passwords, unsecured internet connections, and outdated software. Once you have identified the vulnerability, you can exploit it to gain access to the account. However, it is important to obtain permission from the account owner before attempting to hack into their account. This will ensure that your actions are legal and ethical.
There are several tools and techniques used in ethical hacking. One of the most common tools is Metasploit, which is an open-source framework that helps identify and exploit vulnerabilities. Other tools include Nmap, which is a port scanner that identifies open ports and their services, and Wireshark, which is a packet sniffer that captures and analyzes network traffic. Additionally, social engineering techniques such as phishing and pretexting can also be used to exploit human weaknesses and gain access to an account.
In conclusion, ethical hacking is a legal and authorized process of identifying and exploiting vulnerabilities in a system or network. It is an important practice that helps improve security and protect personal and sensitive information. However, it is important to obtain permission from the account owner before attempting to hack into their account. Ethical hacking is not about breaking laws or violating someone's privacy but is instead about enhancing security and preventing malicious attacks. By following ethical practices and using the right tools and techniques, ethical hacking can be an effective way to enhance security and protect sensitive information.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
A notification pops up on the smartphone screen: "We detected an unusual login attempt from Rio de Janeiro, Brazil. " The first reaction is panic, especially if you live in, say, Vladivostok. What could it be? System failure? Or is someone from the other side of the world really encroaching on your account?
" The first reaction is panic, especially if you live in, say, Vladivostok. What could it be? System failure? Or is someone from the other side of the world really encroaching on your account?
There is no way to panic in such a situation - this will only play into the hands of the burglars. So that you can remain calm and survive this incident with minimal losses, we will arm you with knowledge: we tell you what the matter might be and how to act.
First, let's figure out how a stranger could gain access to your account at all. There are several options here.
A third party site where you registered might have been leaked. Having acquired a list of logins, e-mail addresses and passwords, scammers use them for a substitution attack, that is, they try to enter stolen credentials on many sites. Unfortunately, many people set the same passwords to protect their accounts in different services - this is what criminals are counting on.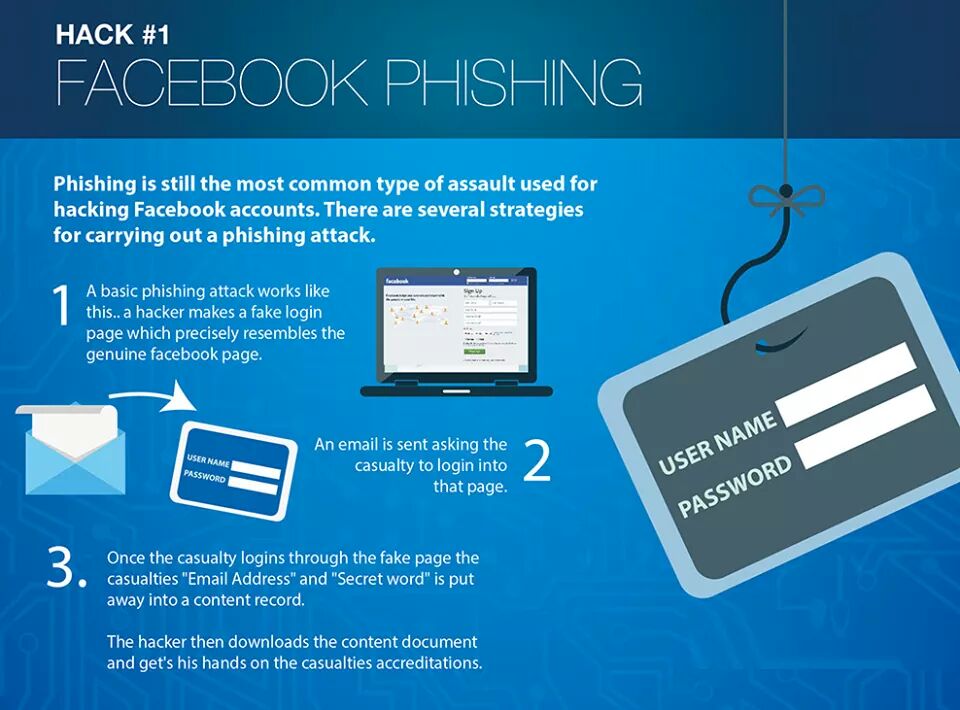
Alternatively, your Facebook or Instagram credentials may have been leaked from the app you trusted them to. For example, in June last year, thousands of passwords from Instagram accounts leaked to the network, the owners of which used the Social Captain service to buy likes and followers. It turned out that he did not encrypt customer data, and anyone could get access to it. It is reasonable to assume that many users of the service have since experienced hacking attempts.
It may also be that some time ago you fell for phishing, and your login with a password fell into the hands of scammers directly. They clicked on some link, and on the page that opened, very similar to the Facebook or Instagram login screen, they entered their credentials. So they ended up with the criminal. For example, most recently, our experts discovered a phishing campaign in which victims were lured to phishing pages by the threat of blocking their Facebook account due to copyright infringement.
Your password may have been stolen by malware you picked up somewhere. Many Trojans have a built-in keylogger, a program that registers keystrokes on the keyboard. All logins and passwords that the victim enters, the keylogger directly passes into the hands of attackers.
Someone may have stolen your access token. So that you don't have to enter a password every time you log into Facebook or Instagram, it saves a small piece of information needed to log in to your computer, which is called a token or access token. If an attacker steals the current token, he will be able to log into the account without a username and password.
Tokens can be stolen in different ways. Sometimes this is done through vulnerabilities in Facebook itself - for example, in 2018, attackers were able to get access tokens to 50 million Facebook accounts. Also, attackers can use browser extensions to steal tokens.
It's possible that you logged into Facebook or Instagram from someone else's device - at a party, in an Internet cafe, in a hotel lobby, and so on - and did not log out after that.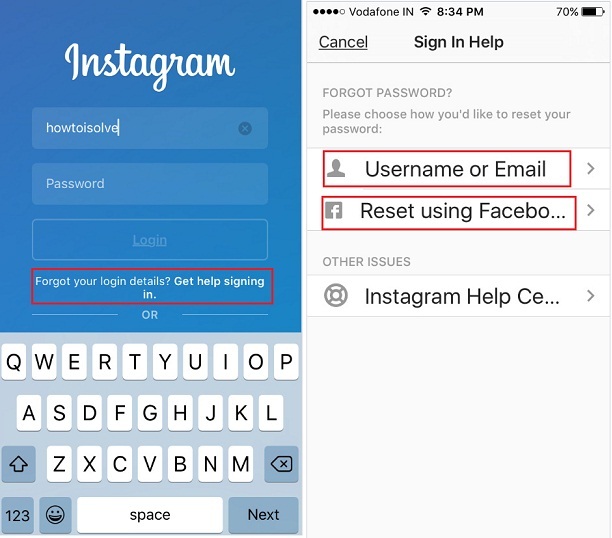 Or, for example, they forgot to log out of their account on a device that they had already sold or donated. Now someone has discovered your oversight and logged into your account.
Or, for example, they forgot to log out of their account on a device that they had already sold or donated. Now someone has discovered your oversight and logged into your account.
Your account may not have been hacked at all, but they are trying with a fake suspicious login notification. This is the same phishing that we talked about above, but a slightly different version of it. Instead of the threat of blocking, scammers can use fake suspicious login notifications with a link to phishing sites similar to the login page. Attackers expect that the victim in a panic will go to a fake site and enter their username and password there.
We have sorted out the possible causes, now it's time to act. To get started, log into your account - but in any case not through the link from the notification (as we already know, it can lead to a phishing site), but through the mobile application or by entering the address in the browser manually. If the password does not match and you can no longer log into your account, refer to the detailed instructions on what to do if your account has already been hijacked, which we published earlier.
If the password does not match and you can no longer log into your account, refer to the detailed instructions on what to do if your account has already been hijacked, which we published earlier.
If you are still allowed into your account, go to your account settings and verify the authenticity of the notification. For each social network, the path to the desired settings item will be different - see how this is done on Facebook and Instagram. Then go to the “Account Logins” section: if there are no suspicious entries there, then everything is in order, and the message about the hack was still phishing.
If you really see a suspicious one in the list of logins to your account, then it's time to hurry up to take protective measures - timely actions will help soften the blow:
 This will reset the access tokens.
This will reset the access tokens. For a smart home to bring you more benefit than harm, it must be properly configured and fully protected. Let's analyze the protection of a smart home in detail.
Let's analyze the protection of a smart home in detail.
Gained a few thousand followers on Instagram? Even more? Congratulations! You are a real celebrity! But in addition to laurels, well-known Insta bloggers have a greater risk of account theft. Not so long ago, scammers invented a new scheme to hijack popular Instagram accounts. We will tell about it now.
"Your account will be permanently deleted due to copyright infringement," the email reads. It looks quite official: here you have both the official header and the Instagram logo, and the sender’s address is very similar to the real one – in most cases it is [email protected] or [email protected].
It looks quite official: here you have both the official header and the Instagram logo, and the sender’s address is very similar to the real one – in most cases it is [email protected] or [email protected].
The notice says you have only 24 hours (48 hours in some versions) to file your appeal. In the letter itself, you will also find a button for appealing the complaint - Review complaint. If you click it, you will be taken to an extremely believable phishing page.
This page tells you how much the service cares about copyright protection. But the most important thing is that there is a link on the page, according to which you can allegedly appeal the deletion of your account. To make everything look even more natural, the page has a long list of language choices, but it's there only for show - whatever you choose, the page is displayed exclusively in English.
After clicking on the account deletion appeal link, you will be prompted to enter your Instagram account information.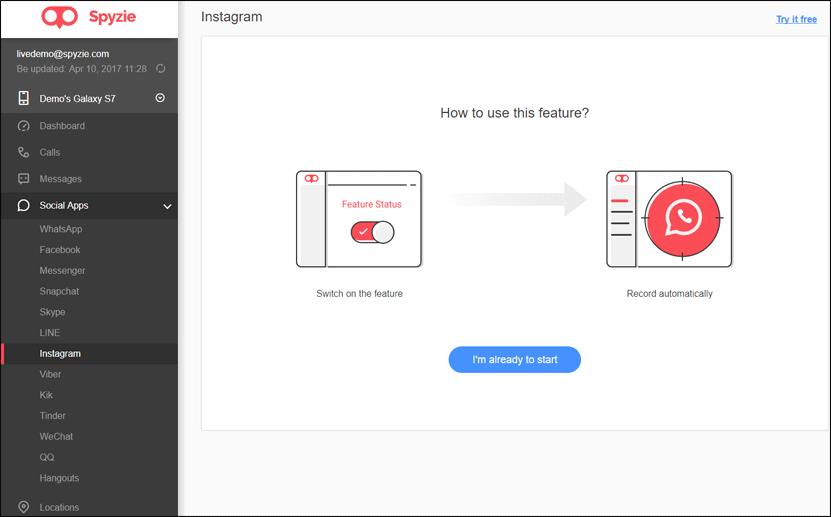 But that's not all - then a new message appears: "We need to authenticate your application and make sure that the email address matches the one specified in Instagram." If you agree to address verification, a list of possible domains will appear on the screen. Selecting one of them, you will see a prompt to enter an email address and (suddenly!) password from it.
But that's not all - then a new message appears: "We need to authenticate your application and make sure that the email address matches the one specified in Instagram." If you agree to address verification, a list of possible domains will appear on the screen. Selecting one of them, you will see a prompt to enter an email address and (suddenly!) password from it.
You will then see a message for just a few seconds that your request is being processed, after which you will be redirected to the real Instagram site. This is another trick that adds credibility to the scam.
This is not the first time popular Instagram users have been targeted by scammers. Recently, a wave of thefts took place under the pretext of obtaining a blue checkmark - a verification badge (Verified Badge).
As soon as your username and password are in the hands of attackers, they will gain access to your Instagram profile and be able to change data to recover it. They can then demand a ransom to get the account back, or start sending spam and other malicious content from it. Not to mention what "open spaces" in front of them will open the password from your email.
They can then demand a ransom to get the account back, or start sending spam and other malicious content from it. Not to mention what "open spaces" in front of them will open the password from your email.
Here are some tips to help keep your Instagram account safe:
