Graham CLULEY
July 15, 2019
Ad One product to protect all your devices, without slowing them down.
Free 90-day trial
A security researcher has been awarded $30,000 after discovering a serious vulnerability that could potentially have put any Instagram account at risk of being hacked.
Following a recent increase in rewards offered for the discovery of critical account takeover vulnerabilities in Facebook and Instagram, Indian security researcher Laxman Muthiyah chose to take a close look at the photo-sharing service.
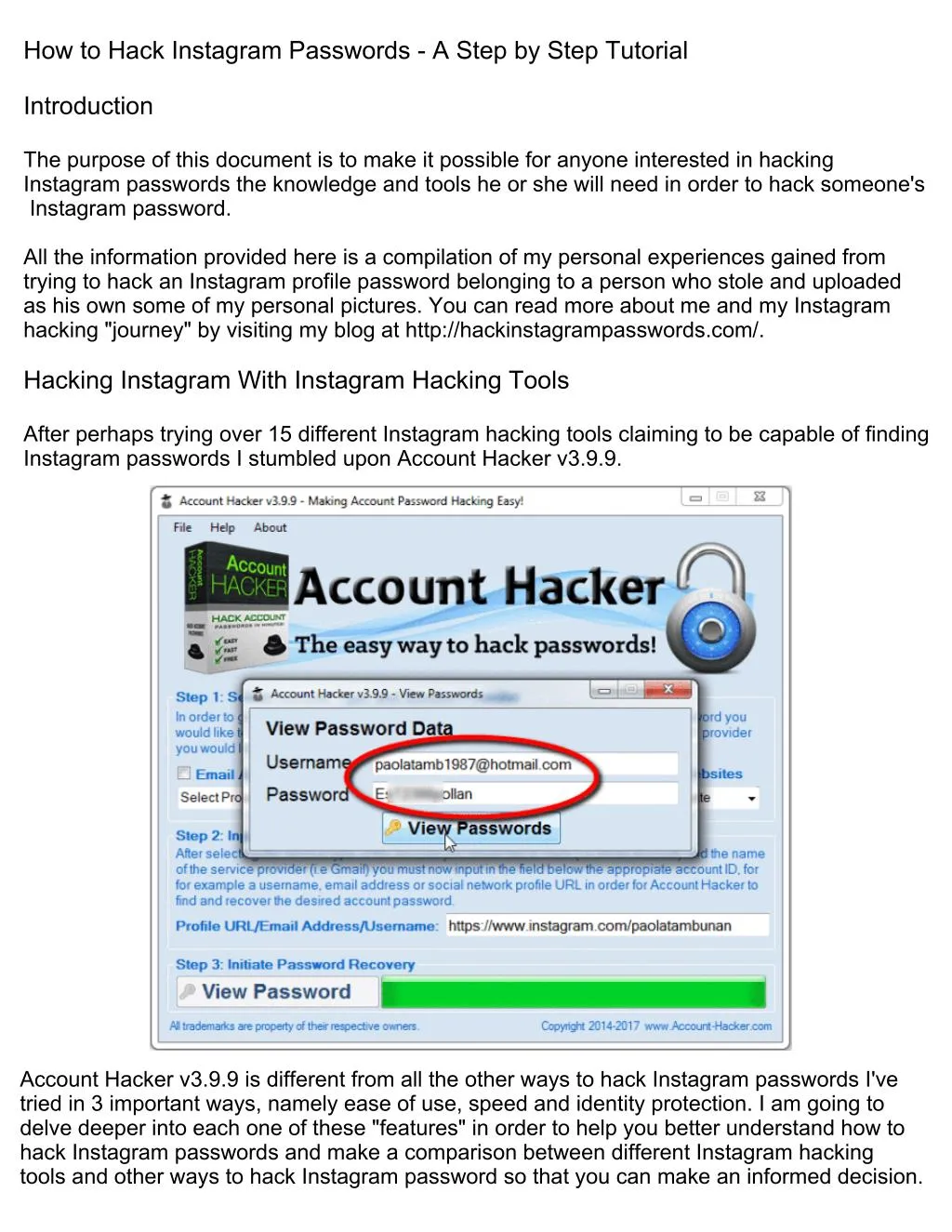
As he describes in a blog post, Muthiyah explored whether there might be a vulnerability in how Instagram handled password reset requests for users who have forgotten their login credentials.
Mutiyah found that when users asked for a password reset via Instagram’s web interface, the site would email a reset link to the user’s email account.
After a few minutes of testing Mutiyah couldn’t find any bugs, and so turned his attention instead to how smartphone users recover access to their Instagram accounts.
What Mutiyah found was that Instagram offered the option for users locked out of their accounts to request that a six-digit secret security code be sent to their mobile phone number or email account. If that passcode is entered, a user can regain access to their Instagram account.
In theory, if a hacker could enter the six-digit security code they would be able to break into the Instagram account (and reset the password locking out the legitimate owner.)
Now, that passcode could potentially be stolen if a hacker had somehow managed to gain access to their target’s email account, or had hijacked control of their victim’s mobile phone number via a SIM swap scam. But Mutiyah wondered if there might be another way to break into accounts if neither of those options were available.
Mutiyah realised that all a hacker would need to do was enter the correct six digit code – a code that could be any combination between 000000 and 999999 – within the ten minute window Instagram would accept the code before expiring it.
Up to one million numbers to be entered within ten minutes, in order to change an Instagram account’s password.
Of course, the likes of Facebook and Instagram aren’t going to simply sit quietly as an automated script tries a brute force attack to guess the correct security code. Instead they have rate-limiting in place to detect when multiple attempts have been made to get past the security check and slow down subsequent attempts – meaning the ten minute window of opportunity expires.
In Mutiyah’s tests he discovered that when he cycled through 1000 attempts to guess an Instagram account’s security codes, 250 of them went through and the subsequent 750 requests were rate limited.
However, after a few days of testing the researcher was able to discover that Instagram’s rate limiting mechanism could be bypassed by rotating IP addresses (in other words, not using the same computer to brute force the recovery code) and sending concurrently from different IP addresses:
“Sending concurrent requests using multiple IPs allowed me to send a large number of requests without getting limited.The number of requests we can send is dependent on concurrency of reqs and the number of IPs we use. Also, I realized that the code expires in 10 minutes, it makes the attack even harder, therefore we need 1000s of IPs to perform the attack.”
Mutiyah says that he used 1000 different machines and IPs to achieve easy concurrency, and sent 200,000 requests in his tests. He shared a YouTube video with Facebook and Instagram’s security team to demonstrate the attack in action:
Of course, 200,000 requests isn’t quite the million requests that would be necessary to guarantee the correct recovery passcode would be entered to allow an Instagram account to be hijacked.
Mutiyah’s investigation concludes that in a real attack, 5000 IP addresses would be needed to hack an Instagram account. Although that sounds like a large number, it can actually be easily achieved at a low price (Mutiyah says there would be approximately US $150 cost if a cloud provider like Google or Amazon was used).
Although that sounds like a large number, it can actually be easily achieved at a low price (Mutiyah says there would be approximately US $150 cost if a cloud provider like Google or Amazon was used).
All Instagram users should be grateful that Laxman Muthiyah chose to responsibly disclose the security vulnerability to Instagram’s security team rather than monetize his discovery by selling it to online criminals.
It’s easy to imagine that a technique like this would be very attractive to many hackers interested in compromising Instagram accounts, and they might be prepared to pay much more than the $30,000 Muthiyah received in the form of a bug bounty.
All internet users are reminded to better secure their online accounts with strong, unique passwords and to enable two-factor authentication wherever possible.
Every year, cybercriminals generate over $3 billion in revenue from social media attacks alone and hacking constitutes a large portion of these malicious incidents.
To help influencers and business owners protect their Instagram accounts, below we breakdown 6 tactics hackers use to extract personal information and bypass 2-factor authentication.
{{learn-more}}
How do hackers hack Instagram accounts? There are default security features on Instagram, like 2-factor authentication, so how can hackers overcome these?
The general answer to that question is, in most cases, some form of social engineering.
In this context, social engineering refers to the act of manipulating and deceiving Instagram users into willingly providing confidential information.
Instagram clearly states that you can only share original content that doesn’t violate copyright infringement laws. That said, it’s possible for you to commit a copyright violation unintentionally, in which case Instagram would take action and reach out to correct the problem.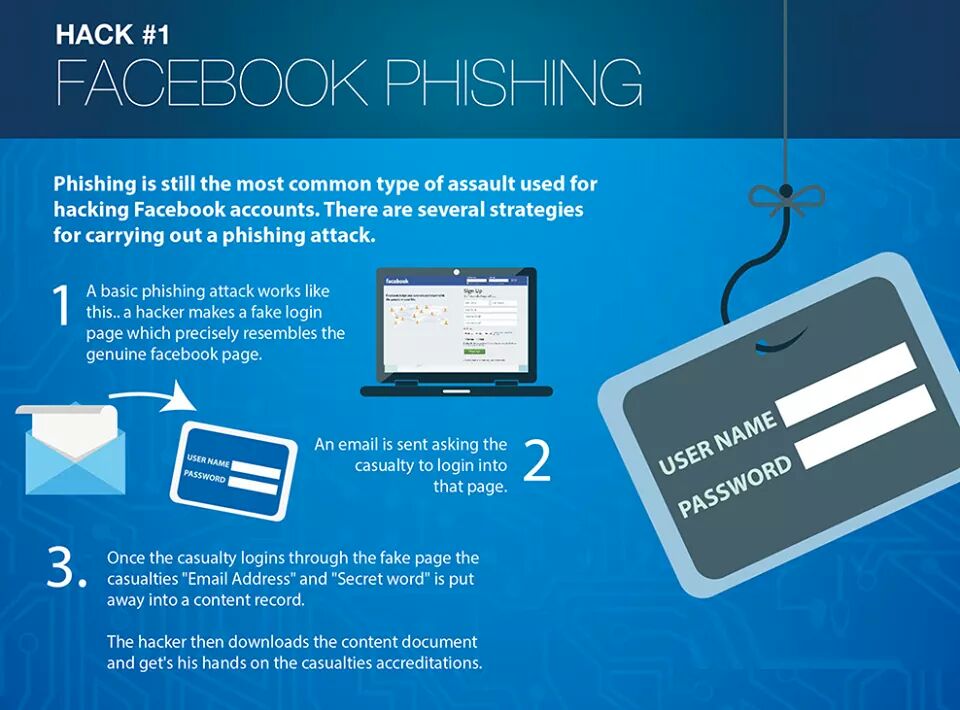
This has led to many cybercriminals actually impersonating Instagram representatives pretending to address copyright infringement issues. In these cases, a hacker sends a link to your email or through a private message on Instagram and asks you to log in in order to address the issue. This is a real-life example of a message that was used to hack @wandertears:
You can learn more about this case by checking out this article.
The link leads to a fake page that, even though it mimics Instagram’s login page, is actually designed to collect your username and password details. The only difference between the real page and the fake is a small variation in the URL, which is hard to detect.
To avoid raising suspicion, cybercriminals usually redirect you to one of Instagram’s legitimate FAQ pages that discusses the topic of copyright infringement.
There’s a couple different methods you can use to verify the messages you receive from Instagram. First, urgent Instagram notifications are usually delivered directly through the account interface or via email. If you receive a DM about your account, it won’t be legitimate - even if it’s from a profile that has the name “Instagram” in the username.
First, urgent Instagram notifications are usually delivered directly through the account interface or via email. If you receive a DM about your account, it won’t be legitimate - even if it’s from a profile that has the name “Instagram” in the username.
Second, Instagram now allows you to see a record of all security and login emails through your account. If you receive a suspicious email directly to your inbox, you should check this part of your Instagram account before opening the message.
From your profile, go to Security>Emails from Instagram. If you don’t see a record of the email, you should delete it right away.
{{subscribe}}
You’re probably familiar with verified badges, the blue pins at the top of Instagram profiles that have been authenticated by the social network. While valuable, this account feature is also at the center of another social engineering that hackers use to break into Instagram.
In this scenario, hackers send a private message or email that offers a chance to add a verified badge, linking to a deceitful website that collects your login information. They may request that you don’t change your profile data, like username or password, until the change has taken effect in order to gain enough time to break into your account.
Here’s an example of a verification badge scam email sent to the owners of pillow business, Cuddle Buddy.
There are a few tell-tell discrepancies here to help you avoid falling for such a scam. For starters, grammar mistakes like excessive capitalization should serve as a warning. Not only this, but the profile the message is being sent from does not belong to an official account nor does it have a verified account. It has the word “Instagram” in the name, but it doesn’t give any indication of being official. Finally, note how the “contact us” text on the blue button is not centered properly, so it’s not consistent with other Instagram content.
To get a blue verification badge right now you need to apply through your profile, and the form you have to fill in should look a little something like this:
Hackers that employ social engineering attacks leverage every piece of information they have at their disposal. For example, they sometimes design suspicious activity alerts that look like a legitimate notification from Instagram, but actually contain malicious links.
According to the Meta-owned social platform, emails from Instagram only come from “@mail.instagram.com” or “@facebookmail.com” addresses. Here’s an example of what a legitimate security email from Instagram looks like:
This security message is for a new login from a device that the user didn’t commonly sign in through. Note how the email address is from a trusted source and how all of the design elements are aligned properly.
Even if the emails you receive look legitimate, we advise that you go to your Instagram account and verify that the security email was sent through there.
Fraudulent giveaways are especially troublesome because they exist in an ecosystem that is packed with legitimate promotional freebies. This form of social engineering can take two different shapes.
In its most traditional version, this type of hack operates like a false verified badge attack. The difference is that the hacker impersonates a big brand, exciting start-up, or similar renowned company that’s offering a big giveaway to specific social media influencers.
Some scammers even have legitimate-looking accounts that have been active for a while and have thousands of followers. The first message usually includes at least one spoofed link leading to a false Instagram login that’s designed to extract the username and password submitted.
A more complex form of fraudulent giveaways and sponsorships can occur when hackers have collected information about you, but still need a few more details to successfully breach your account. Instead of sending you a link to a spoofed login page, hackers may ask you to fill in a survey that asks for personal information, like your date of birth, mother’s maiden name, and other answers to common security questions.
Instead of sending you a link to a spoofed login page, hackers may ask you to fill in a survey that asks for personal information, like your date of birth, mother’s maiden name, and other answers to common security questions.
Below is a real example of the phishing email that led to @FlipFlopWanderers getting hacked. Read their full story here.
Never rush or feel pressured into clicking links. Take time to investigate if the email looks legitimate: for instance, check for spelling mistakes and hover over the hyperlink to see if the URL leads to a familiar or safe website. To be extra safe, you could even Google the company supposedly sending the email, and contact them to check if they really did send you an email.
Managing a social media profile can take a huge amount of time, especially if you have a large base of followers. There are many tools that can simplify the process, but you also have to evaluate each platform to make sure it comes from a legitimate developer.
Just as with malicious web extensions, hackers can create counterfeit tools that are supposed to improve functionality, but actually pose a security threat.
These tools usually look and feel legitimate, but bring you very little in terms of functionality and practical value. This type of scheme is not as common because it requires a significant amount of resources, but it’s still used by cybercriminals looking for bigger, more valuable targets.
When this type of attack is successful, target users integrate the counterfeit tool into their social media accounts. This fake tool can be used to set up man-in-the-middle attacks, intercept all data, and extract login details, among other data.
It’s normal to watch your budget, especially in the early stages of your Instagram account. But, working with lesser-known, low-cost tools increases the chances of being targeted by scammers. To avoid this, you should opt for established tools that come from renowned providers or platforms that have been recommended by trusted peers.
All of the social engineering hacking techniques we’ve covered so far require hackers to manually create fake apps and website pages in order to collect details from their targets. With reverse proxy attacks, hackers don’t need to create a spoof website or app - instead they can automate the theft of credentials.
A reverse proxy attack is a type of man-in-the-middle approach - hackers direct victims to a domain that sits in between the user and the legitimate website. The URL will be very similar to the legitimate page, and the overall appearance in the malicious domain mirrors the legitimate page.
When applied to the Instagram context, you could receive a convincing email from a hacker that directs you to Instagram’s login page. What you don’t realize is that you’ve been sent to do this via a proxy server - so when you enter your credentials and log into Instagram, your information - including 2FA - is being intercepted in real time.
Be extremely cautious when clicking on links from your email inbox - always verify an email claiming to be from Instagram by checking your Instagram account. From your profile, go to Security>Emails - if the email doesn’t appear there, it’s likely a scam.
Now that we’ve answered the question “how do hackers steal Instagram accounts?” let's go over the reasons why these criminals may want to target your profile.
Like other types of criminals, hackers and other malicious actors flock to the most popular platforms because these present the biggest financial opportunities. Today, you can generate a significant amount of revenue from a large base of followers and hackers are eager to benefit from this.
Some of the common things a hacker may do once your account is breached include:
Hackers use a wide range of approaches and develop new techniques regularly to bypass Instagram’s default security measures. The number of social media scam victims in the US skyrocketed from 46,000 to 95,000 in 2021, and that number shows no signs of slowing down in the near future.
Learning about the different techniques that hackers use and implementing security best practices as a counter are the first steps to keeping your Instagram account safe. Unfortunately, however, there is no way to guarantee your account against hacks - even users with multi factor authentication set up are falling victim. That's why we launched Notch - to finally give creators peace of mind.
{{learn-more}}
A notification pops up on the smartphone screen: "We detected an unusual login attempt from Rio de Janeiro, Brazil. " The first reaction is panic, especially if you live in, say, Vladivostok. What could it be? System failure? Or is someone from the other side of the world really encroaching on your account?
" The first reaction is panic, especially if you live in, say, Vladivostok. What could it be? System failure? Or is someone from the other side of the world really encroaching on your account?
There is no way to panic in such a situation - this will only play into the hands of the burglars. So that you can remain calm and survive this incident with minimal losses, we will arm you with knowledge: we tell you what the matter might be and how to act.
First, let's figure out how a stranger could gain access to your account at all. There are several options here.
A third party site where you registered might have been leaked. Having acquired a list of logins, e-mail addresses and passwords, scammers use them for a substitution attack, that is, they try to enter stolen credentials on many sites. Unfortunately, many people set the same passwords to protect their accounts in different services - this is what criminals are counting on.
Alternatively, your Facebook or Instagram credentials may have been leaked from the app you trusted them to. For example, in June last year, thousands of passwords from Instagram accounts leaked to the network, the owners of which used the Social Captain service to buy likes and followers. It turned out that he did not encrypt customer data, and anyone could get access to it. It is reasonable to assume that many users of the service have since experienced hacking attempts.
It may also be that some time ago you fell for phishing, and your login with a password fell into the hands of scammers directly. They clicked on some link, and on the page that opened, very similar to the Facebook or Instagram login screen, they entered their credentials. So they ended up with the criminal. For example, most recently, our experts discovered a phishing campaign in which victims were lured to phishing pages by the threat of blocking their Facebook account due to copyright infringement.
Your password may have been stolen by malware you picked up somewhere. Many Trojans have a built-in keylogger, a program that registers keystrokes on the keyboard. All logins and passwords that the victim enters, the keylogger directly passes into the hands of attackers.
Someone may have stolen your access token. So that you don't have to enter a password every time you log into Facebook or Instagram, it saves a small piece of information needed to log in to your computer, which is called a token or access token. If an attacker steals the current token, he will be able to log into the account without a username and password.
Tokens can be stolen in different ways. Sometimes this is done through vulnerabilities in Facebook itself - for example, in 2018, attackers were able to get access tokens to 50 million Facebook accounts. Also, attackers can use browser extensions to steal tokens.
It's possible that you logged into Facebook or Instagram from someone else's device - at a party, in an Internet cafe, in a hotel lobby, and so on - and did not log out after that. Or, for example, they forgot to log out of their account on a device that they had already sold or donated. Now someone has discovered your oversight and logged into your account.
Or, for example, they forgot to log out of their account on a device that they had already sold or donated. Now someone has discovered your oversight and logged into your account.
Your account may not have been hacked at all, but they are trying with a fake suspicious login notification. This is the same phishing that we talked about above, but a slightly different version of it. Instead of the threat of blocking, scammers can use fake suspicious login notifications with a link to phishing sites similar to the login page. Attackers expect that the victim in a panic will go to a fake site and enter their username and password there.
We have sorted out the possible causes, now it's time to act. To get started, log into your account - but in any case not through the link from the notification (as we already know, it can lead to a phishing site), but through the mobile application or by entering the address in the browser manually. If the password does not match and you can no longer log into your account, refer to the detailed instructions on what to do if your account has already been hijacked, which we published earlier.
If the password does not match and you can no longer log into your account, refer to the detailed instructions on what to do if your account has already been hijacked, which we published earlier.
If you are still allowed into your account, go to your account settings and verify the authenticity of the notification. For each social network, the path to the desired settings item will be different - see how this is done on Facebook and Instagram. Then go to the “Account Logins” section: if there are no suspicious entries there, then everything is in order, and the message about the hack was still phishing.
If you really see a suspicious one in the list of logins to your account, then it's time to hurry up to take protective measures - timely actions will help soften the blow:
 This will reset the access tokens.
This will reset the access tokens. We tell how scammers deceive users of a well-known marketplace using a fake product payment page.
Hello everyone. I am the marketing manager for Picalytics Instagram analytics and I decided to write an article for marketers and business owners, because in my work I encounter banal non-compliance with safety precautions several times a week.
Let's say you spent time and money promoting your account, rebuilt your direct sales process, and got loyal customers. In the morning, you open Instagram to launch a promotion and... you can't log in to your account. In this article, you will learn about the “prevention” of hacking and what to do if your account is stolen.
You can register on Instagram through mail, Facebook or by phone number. With access to your smartphone (and therefore Facebook, mail), it is easy to access all the services associated with them. Therefore, they steal accounts through these "entry points".
First of all, check the relevance and security of the services linked to your account. Then make sure that you have not specified the mail associated with the account in the contact methods.
And one more thing: you don't store accesses in Google Docs or notes on your smartphone, do you?
In addition to mail and phone theft, the most common hacking option is phishing (gaining access) to the account directly:
This is the usual copying of mail and official letters from Instagram. In this case, the attacker sends a letter that looks as close as possible to a letter from Instagram - both in interface design and in the sender's address.
The screenshots below show examples of emails from Instagram.
The role address can be different - you need to pay attention to the domain name (the part after @).
This is how a letter from scammers looks like.
Cloned phishing is designed for inattentive people and novice account administrators. Therefore, look both ways when you follow unknown links.
Business stories and useful features
As a rule, these are photo editors, promotion automation, auto-posting, direct web versions and so on.
Phishing apps are not verified by Google Play and AppStore. Such services, when registering, request access to an account or imitate authorization through Instagram.
Do not be afraid of authorization in third-party services: some options are not possible without access to the account.
Remember: authorization through Instagram takes place in a new tab on the official website of Instagram.
To check the list of applications that have access to your account, go to the application settings and click "Access Management". You have logged in to these applications through Instagram and can revoke access to your account from them.
If you have lost your smartphone or tablet with access to your account, change your password from Instagram and the service linked to it (mail or Facebook) as soon as possible.
In most cases, small Instagram accounts are hacked to be sold to third parties. On average, such "dead souls" cost $0.3-0.5.
In our experience with Instagram tech support, there is no relationship between account size (or ad budget) and response speed.
For example, after a major advertising campaign, we saw a duplicate account using our trademark (which is a serious violation) and wrote to technical support. There has been no response from Instagram for three weeks. But there are exceptions to the rule.
But there are exceptions to the rule.
Try to react quickly. If you can still log in to your account, change the password for the linked services (mail and / or Facebook). Then enable two-factor authentication.
If you can't log in to your account over , try resetting your password via mail, Facebook or phone number. Upon successful login, enable two-factor authentication.
If you do not receive notifications from Instagram when resetting your password and cannot log in via Facebook (if it was connected), then your account was linked to another mail, and also unlinked from Facebook and a phone number (if if they were connected).
In this case, we recommend that you send a request to Instagram support:

Instagram can substitute in the phone number field the number of the SIM card currently in the phone - this is not always the number associated with the account.
By the way, we never received a magic link via SMS, despite the fact that the accounts were linked to a phone number.
If you did not receive a letter to your address or your nickname was changed, repeat the previous paragraph by entering both nickname and mail.
If you can't find your account using your old nickname anymore, look in your inbox for emails from Instagram. Didn't receive any information about the account change? Ask a friend to find out your current nickname through the history of correspondence in direct or from comments previously left on your behalf.
If you succeeded in logging in, change the password for your account and associated services (mail and/or Facebook). Then enable two-factor authentication.
1. On the password recovery page, click "Need more help?" and enter all the requested information. Check the box next to "My account has been hacked". Send a request and wait for a response to the specified mail.
On the password recovery page, click "Need more help?" and enter all the requested information. Check the box next to "My account has been hacked". Send a request and wait for a response to the specified mail.
2. If you do not receive a response within a few days, repeat the request by checking the box next to "I forgot the mail associated with my account."
If you managed to regain access to your account, you can change your nickname to any free one. Including your old nickname, if it has been changed.
In some cases, the condition for restoring access to the account by Instagram may be a change of nickname. In this situation, we recommend using a nickname that is as close as possible to the previous one: for example, add a dot or underscore.
If your account has been deleted, you can create a new account with the same email address, but you may not be able to use your old username.
 Most likely, the account will not be returned or you will be asked to pay extra (and pay a little more).
Most likely, the account will not be returned or you will be asked to pay extra (and pay a little more). Hacking an account without the help of its owner is a difficult task. Don't let a moment of inattention deprive you of months of work on your account.
How to insure your account: