Graham CLULEY
July 15, 2019
Ad One product to protect all your devices, without slowing them down.
Free 90-day trial
A security researcher has been awarded $30,000 after discovering a serious vulnerability that could potentially have put any Instagram account at risk of being hacked.
Following a recent increase in rewards offered for the discovery of critical account takeover vulnerabilities in Facebook and Instagram, Indian security researcher Laxman Muthiyah chose to take a close look at the photo-sharing service.
As he describes in a blog post, Muthiyah explored whether there might be a vulnerability in how Instagram handled password reset requests for users who have forgotten their login credentials.
Mutiyah found that when users asked for a password reset via Instagram’s web interface, the site would email a reset link to the user’s email account.
After a few minutes of testing Mutiyah couldn’t find any bugs, and so turned his attention instead to how smartphone users recover access to their Instagram accounts.
What Mutiyah found was that Instagram offered the option for users locked out of their accounts to request that a six-digit secret security code be sent to their mobile phone number or email account. If that passcode is entered, a user can regain access to their Instagram account.
In theory, if a hacker could enter the six-digit security code they would be able to break into the Instagram account (and reset the password locking out the legitimate owner.)
Now, that passcode could potentially be stolen if a hacker had somehow managed to gain access to their target’s email account, or had hijacked control of their victim’s mobile phone number via a SIM swap scam. But Mutiyah wondered if there might be another way to break into accounts if neither of those options were available.
Mutiyah realised that all a hacker would need to do was enter the correct six digit code – a code that could be any combination between 000000 and 999999 – within the ten minute window Instagram would accept the code before expiring it.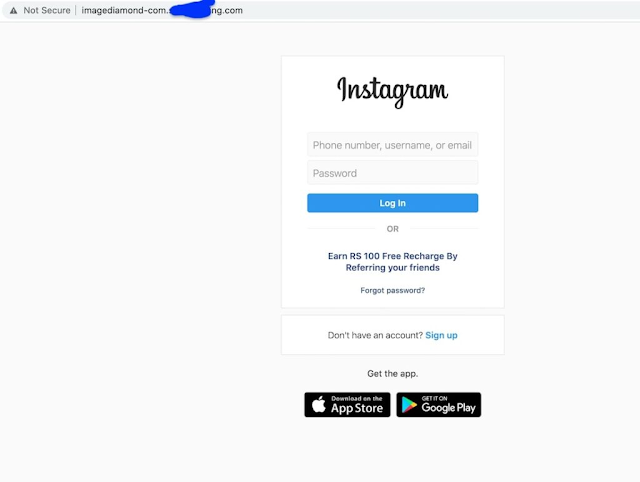
Up to one million numbers to be entered within ten minutes, in order to change an Instagram account’s password.
Of course, the likes of Facebook and Instagram aren’t going to simply sit quietly as an automated script tries a brute force attack to guess the correct security code. Instead they have rate-limiting in place to detect when multiple attempts have been made to get past the security check and slow down subsequent attempts – meaning the ten minute window of opportunity expires.
In Mutiyah’s tests he discovered that when he cycled through 1000 attempts to guess an Instagram account’s security codes, 250 of them went through and the subsequent 750 requests were rate limited.
However, after a few days of testing the researcher was able to discover that Instagram’s rate limiting mechanism could be bypassed by rotating IP addresses (in other words, not using the same computer to brute force the recovery code) and sending concurrently from different IP addresses:
“Sending concurrent requests using multiple IPs allowed me to send a large number of requests without getting limited.The number of requests we can send is dependent on concurrency of reqs and the number of IPs we use. Also, I realized that the code expires in 10 minutes, it makes the attack even harder, therefore we need 1000s of IPs to perform the attack.”
Mutiyah says that he used 1000 different machines and IPs to achieve easy concurrency, and sent 200,000 requests in his tests. He shared a YouTube video with Facebook and Instagram’s security team to demonstrate the attack in action:
Of course, 200,000 requests isn’t quite the million requests that would be necessary to guarantee the correct recovery passcode would be entered to allow an Instagram account to be hijacked.
Mutiyah’s investigation concludes that in a real attack, 5000 IP addresses would be needed to hack an Instagram account. Although that sounds like a large number, it can actually be easily achieved at a low price (Mutiyah says there would be approximately US $150 cost if a cloud provider like Google or Amazon was used).
Although that sounds like a large number, it can actually be easily achieved at a low price (Mutiyah says there would be approximately US $150 cost if a cloud provider like Google or Amazon was used).
All Instagram users should be grateful that Laxman Muthiyah chose to responsibly disclose the security vulnerability to Instagram’s security team rather than monetize his discovery by selling it to online criminals.
It’s easy to imagine that a technique like this would be very attractive to many hackers interested in compromising Instagram accounts, and they might be prepared to pay much more than the $30,000 Muthiyah received in the form of a bug bounty.
All internet users are reminded to better secure their online accounts with strong, unique passwords and to enable two-factor authentication wherever possible.
When you hear "security breach," what springs to mind? A malevolent hacker sitting in front of screens covered in Matrix-style digital text? Or a basement-dwelling teenager who hasn't seen daylight in three weeks? How about a powerful supercomputer attempting to hack the entire world?
Hacking is all about one thing: your password. If someone can guess your password, they don't need fancy hacking techniques and supercomputers. They'll just log in, acting as you. If your password is short and simple, it's game over.
If someone can guess your password, they don't need fancy hacking techniques and supercomputers. They'll just log in, acting as you. If your password is short and simple, it's game over.
There are eight common tactics hackers use to hack your password.
First up in the common password hacking tactics guide is the dictionary attack. Why is it called a dictionary attack? Because it automatically tries every word in a defined "dictionary" against the password. The dictionary isn't strictly the one you used in school.
No. This dictionary is actually a small file containing the most commonly used password combinations. That includes 123456, qwerty, password, iloveyou, and the all-time classic, hunter2.
The above table details the most leaked passwords in 2016. The below table details the most leaked passwords in 2020.
Note the similarities between the two—and make sure you don't use these incredibly simple options. And for those wondering why this leaked password list hasn't been updated since 2020, it's simply because the weak, awful passwords remain the same, just in a slightly different order. Long story short, if you don't want someone to figure out your password, never use any of these.
Long story short, if you don't want someone to figure out your password, never use any of these.
Next up is the brute force attack, whereby an attacker tries every possible character combination in an attempt to guess your password. Attempted passwords will match the specifications for the complexity rules, e.g., including one upper-case, one lower-case, decimals of Pi, your pizza order, and so on.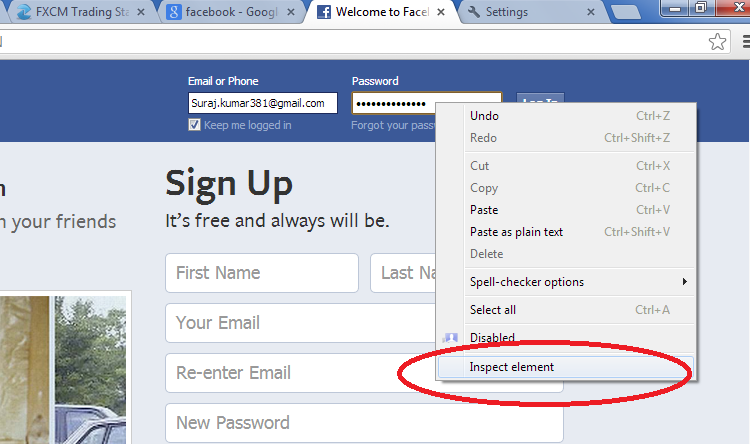
A brute force attack will also try the most commonly used alphanumeric character combinations first, too. These include the previously listed passwords, as well as 1q2w3e4r5t, zxcvbnm, and qwertyuiop. It can take a very long time to figure out a password using this method, but that depends entirely on password complexity.
This isn't strictly a "hack," but falling prey to a phishing or spear-phishing attempt will usually end badly. General phishing emails are sent by the billions to all manner of internet users around the globe, and it is definitely one of the most popular ways to find out someone's password.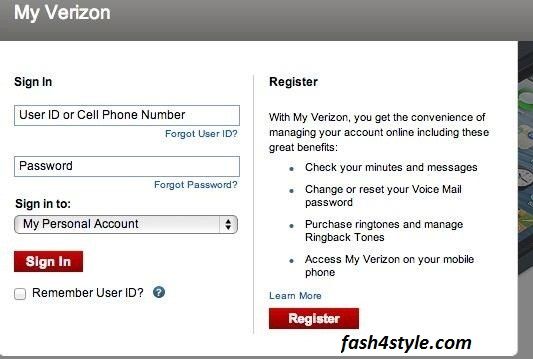
A phishing email generally works like this:
The daily spam volume sent worldwide remains high, accounting for over half of all emails sent globally. Furthermore, the volume of malicious attachments is high, too, with Kaspersky blocking over 148 million malicious attachments in 2021. Furthermore, Kaspersky's Anti-Phishing system blocked an additional 253 million phishing links. Remember, this is just for Kaspersky, so the real number is much higher.
4 Images
Back in 2017, the biggest phishing lure was a fake invoice. However, in 2020, the COVID-19 pandemic provided a new phishing threat. In April 2020, not long after many countries went into pandemic lockdown, Google announced it was blocking over 18 million COVID-19-themed malicious spam and phishing emails per day. Huge numbers of these emails use official government or health organization branding for legitimacy and catch victims off-guard.
 Use a link checker to ascertain if an email link is legitimate before clicking.
Use a link checker to ascertain if an email link is legitimate before clicking. Social engineering is essentially phishing in the real world, away from the screen.
A core part of any security audit is gauging what the entire workforce understands. For instance, a security company will phone the business they are auditing. The "attacker" tells the person on the phone they are the new office tech support team, and they need the latest password for something specific.
An unsuspecting individual may hand over the keys without a pause for thought.
The scary thing is how often this works. Social engineering has existed for centuries. Being duplicitous to gain entry to a secure area is a common method of attack and one that is only guarded against with education. This is because the attack won't always ask directly for a password. It could be a fake plumber or electrician asking for entry to a secure building, and so on. When someone says they were tricked into revealing their password, it is often the result of social engineering.
A rainbow table is usually an offline password attack. For example, an attacker has acquired a list of user names and passwords, but they're encrypted. The encrypted password is hashed. This means it looks completely different from the original password.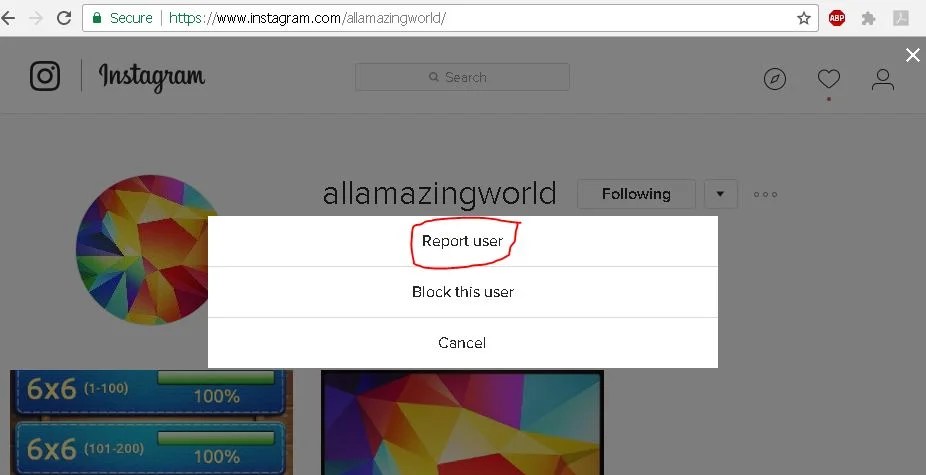
For instance, your password is (hopefully not!) logmein. The known MD5 hash for this password is "8f4047e3233b39e4444e1aef240e80aa."
Gibberish to you and I. But in certain cases, the attacker will run a list of plaintext passwords through a hashing algorithm, comparing the results against an encrypted password file. In other cases, the encryption algorithm is vulnerable, and most passwords are already cracked, like MD5 (hence why we know the specific hash for "logmein."
This is where the rainbow table comes into its own. Instead of having to process hundreds of thousands of potential passwords and matching their resulting hash, a rainbow table is a huge set of precomputed algorithm-specific hash values. Using a rainbow table drastically decreases the time it takes to crack a hashed password—but it isn't perfect. Hackers can purchase prefilled rainbow tables populated with millions of potential combinations.

Another sure way to lose your login credentials is to fall foul of malware. Malware is everywhere, with the potential to do massive damage. If the malware variant features a keylogger, you could find all of your accounts compromised.
Alternatively, the malware could specifically target private data or introduce a remote access Trojan to steal your credentials.
 A good chance a high number of targets will succumb to at least one variant. It can go undetected, allowing further harvesting of private data and login credentials.
A good chance a high number of targets will succumb to at least one variant. It can go undetected, allowing further harvesting of private data and login credentials. Spidering ties into the dictionary attack. If a hacker targets a specific institution or business, they might try a series of passwords relating to the business itself. The hacker could read and collate a series of related terms—or use a search spider to do the work for them.
You might have heard the term "spider" before. These search spiders are extremely similar to those that crawl through the internet, indexing content for search engines. The custom word list is then used against user accounts in the hope of finding a match.
These search spiders are extremely similar to those that crawl through the internet, indexing content for search engines. The custom word list is then used against user accounts in the hope of finding a match.
The final option is one of the most basic. What if someone just looks over your shoulder while you're typing in your password?
Shoulder surfing sounds a little ridiculous, but it does happen. If you're working in a busy downtown café and not paying attention to your surroundings, someone could get close enough to note your password as you type, but it's probably not the easiest way to figure out someones password.
So, how do you stop a hacker from stealing your password? The really short answer is that you cannot truly be 100 percent safe. The tools hackers use to steal your data are changing all the time and there are countless videos and tutorials on guessing passwords or learning how to hack a password, or even just how to figure out someone's password.
One thing is for sure: using a strong, unique, single-use password never hurt anyone.
A notification pops up on the smartphone screen: "We detected an unusual login attempt from Rio de Janeiro, Brazil.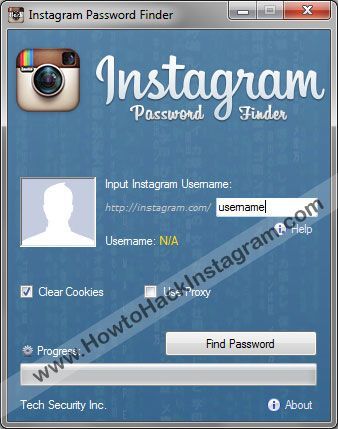 " The first reaction is panic, especially if you live in, say, Vladivostok. What could it be? System failure? Or is someone from the other side of the world really encroaching on your account?
" The first reaction is panic, especially if you live in, say, Vladivostok. What could it be? System failure? Or is someone from the other side of the world really encroaching on your account?
There is no way to panic in such a situation - this will only play into the hands of the burglars. So that you can remain calm and survive this incident with minimal losses, we will arm you with knowledge: we tell you what the matter might be and how to act.
First, let's figure out how a stranger could gain access to your account at all. There are several options here.
A third party site where you registered might have been leaked. Having acquired a list of logins, e-mail addresses and passwords, scammers use them for a substitution attack, that is, they try to enter stolen credentials on many sites. Unfortunately, many people set the same passwords to protect their accounts in different services - this is what criminals are counting on.
Alternatively, your Facebook or Instagram credentials may have been leaked from the app you trusted them to. For example, in June last year, thousands of passwords from Instagram accounts leaked to the network, the owners of which used the Social Captain service to buy likes and followers. It turned out that he did not encrypt customer data, and anyone could get access to it. It is reasonable to assume that many users of the service have since experienced hacking attempts.
It may also be that some time ago you fell for phishing, and your login with a password fell into the hands of scammers directly. They clicked on some link, and on the page that opened, very similar to the Facebook or Instagram login screen, they entered their credentials. So they ended up with the criminal. For example, most recently, our experts discovered a phishing campaign in which victims were lured to phishing pages by the threat of blocking their Facebook account due to copyright infringement.
Your password may have been stolen by malware you picked up somewhere. Many Trojans have a built-in keylogger, a program that registers keystrokes on the keyboard. All logins and passwords that the victim enters, the keylogger directly passes into the hands of attackers.
Someone may have stolen your access token. So that you don't have to enter a password every time you log into Facebook or Instagram, it saves a small piece of information needed to log in to your computer, which is called a token or access token. If an attacker steals the current token, he will be able to log into the account without a username and password.
Tokens can be stolen in different ways. Sometimes this is done through vulnerabilities in Facebook itself - for example, in 2018, attackers were able to get access tokens to 50 million Facebook accounts. Also, attackers can use browser extensions to steal tokens.
It's possible that you logged into Facebook or Instagram from someone else's device - at a party, in an Internet cafe, in a hotel lobby, and so on - and did not log out after that.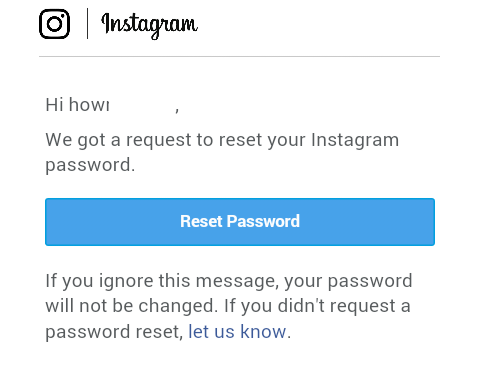 Or, for example, they forgot to log out of their account on a device that they had already sold or donated. Now someone has discovered your oversight and logged into your account.
Or, for example, they forgot to log out of their account on a device that they had already sold or donated. Now someone has discovered your oversight and logged into your account.
Your account may not have been hacked at all, but they are trying with a fake suspicious login notification. This is the same phishing that we talked about above, but a slightly different version of it. Instead of the threat of blocking, scammers can use fake suspicious login notifications with a link to phishing sites similar to the login page. Attackers expect that the victim in a panic will go to a fake site and enter their username and password there.
We have sorted out the possible causes, now it's time to act. To get started, log into your account - but in any case not through the link from the notification (as we already know, it can lead to a phishing site), but through the mobile application or by entering the address in the browser manually.
If you are still allowed into your account, go to your account settings and verify the authenticity of the notification. For each social network, the path to the desired settings item will be different - see how this is done on Facebook and Instagram. Then go to the “Account Logins” section: if there are no suspicious entries there, then everything is in order, and the message about the hack was still phishing.
If you really see a suspicious one in the list of logins to your account, then it's time to hurry up to take protective measures - timely actions will help soften the blow:
 This will reset the access tokens.
This will reset the access tokens. Avast solutions have a good reputation, but several incidents cast doubt on their reliability.
How to watch the World Cup without becoming a victim of scammers.
Fraudsters pretend to be government officials in emails to swindle users of their personal data and money.
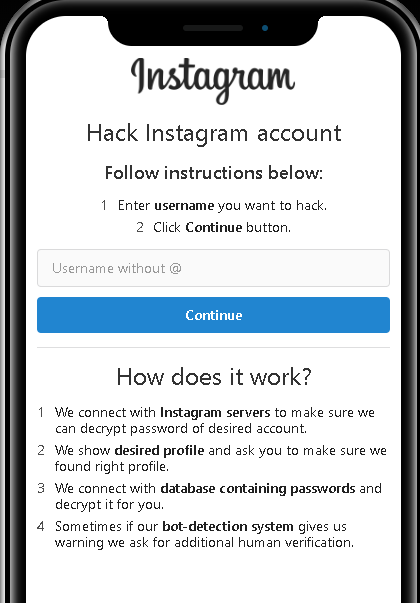
Don't know how to hack a password (page, profile) from Instagram? Looking for a reliable Instagram account hack to read correspondence and see photos? Reliable 5 Ways to Hack Insta - It's not as hard as you think!
Instagram hacking is an illegal act that can deprive you of a decent amount of money in the form of a fine and even reward you with a real prison term. Therefore, before doing something in this area, think about it, is it really so important and necessary for you?
Therefore, before doing something in this area, think about it, is it really so important and necessary for you?
We start with the simplest and most realistic (which can be used by everyone without exception) way to hack Instagram - you need to take only 10 (! ) minutes phone and quickly there download free Reptilicus , install and configure. This is easy enough to do. Everything is in Russian. Extremely understandable. If you have any questions, the site has picture guide , instruction video, as well as online consultants.
After installing the application you will be able to:
All this will become available when you install the special Reptilicus application on your phone. We offer not hacking an Instagram account, but control - this is the ability to remotely control a person's activities in this social network without penetrating his page and without performing any illegal actions combined with hacking.
In simple words, you won't need to hack your Instagram profile, you just install the program on your phone, and the program itself will send you everything that a person does on his phone, including on his page on Instagram.
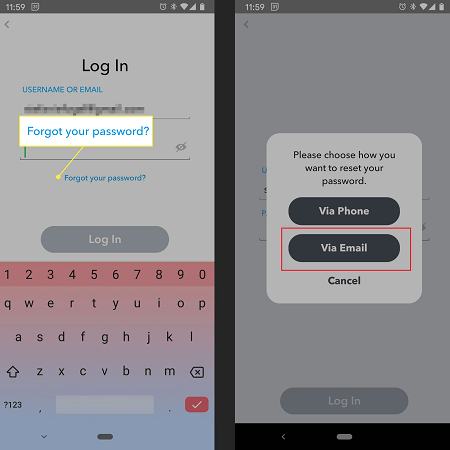
We continue our review ... this is the most obvious method that (we don’t know for what reason) people don’t see on their own, although it lies on the surface. Yes, imagine, you can crack the Instagram password in order to get into the page using a function that allows you to recover a forgotten password. Here you need to know only the login (nickname) of the person. Just? Yes! Why didn't you think of this before? We do not know! So, you need to take the following steps:
Just? Yes! Why didn't you think of this before? We do not know! So, you need to take the following steps:
Step 1. If you have your own page, then go to your account - click on the Instagram icon - the home page will open. If not, then just go through the search engine.
Step 2. Press "Menu" - press "Add Account" - the standard menu for logging into your account will open.
Step 3. Enter the username (nickname/login) - click "Forgot Password".
Step 4. Select confirmation via SMS - enter your phone number - wait for SMS with a link to change your password.
Step 5. Open SMS - in the Change Password section, click on change password - change password.
That's it, now you know how to crack your Instagram password! No need to thank.
You have probably heard that there are programs that can save keystrokes on your phone.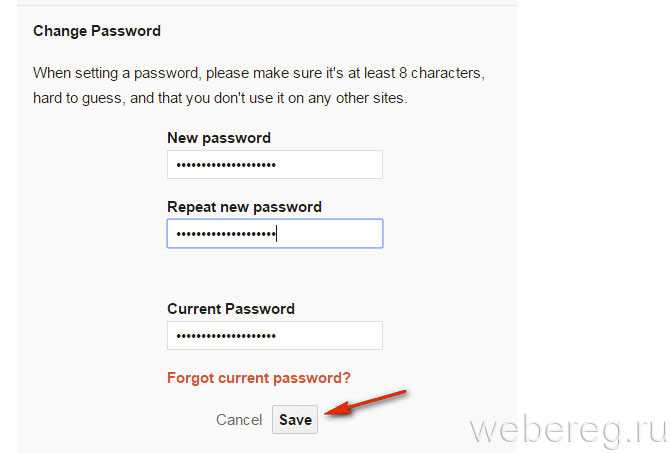 And if you are thinking about how to hack an account on Instagram, then this method can allow you to intercept messages typed on your phone when communicating on Instagram.
And if you are thinking about how to hack an account on Instagram, then this method can allow you to intercept messages typed on your phone when communicating on Instagram.
The Reptilicus program will help you to see literally everything that the person whose correspondence you are so interested in is typing on his phone. You can also install any other keylogger, of which there are quite a lot on the Internet. We are just talking about our program, tested by time and users. You can hack an Instagram page with a simple installation. There are reviews of real users (the forum is over 7 years old).
Chat screenshots, screenshots or instant screenshots (call it what you want, the meaning of this will not change in any way) is a real opportunity to do without the treacherous hacking of Insta. The screenshots will show all the correspondence, with emoticons, with all the actions that a person performs on his phone.
Screenshots are taken automatically and without root rights, as well as keyboard interception. They will start coming as soon as a person goes to the page on Insta. To do this, you need to check the box in the program settings so that screenshots start working when you enter Instagram.
They will start coming as soon as a person goes to the page on Insta. To do this, you need to check the box in the program settings so that screenshots start working when you enter Instagram.
If you want to receive screenshots around the clock, and not just when you enter Insta, then do not set any restrictions. The settings are very convenient - make sure by looking at the manual. You can do this, but you can do that. Adjust as you need. If you want to receive screenshots every 10 seconds, get it, if you want only correspondence, please, receive only correspondence. Here the choice is entirely yours.
This method is considered the easiest, but at the same time the most illegal. This is a gross scam. Therefore, we do not advise you to use it. BUT since we provide possible ways, phishing will help you understand how to hack Instagram through a computer.
This method is that you create a phishing (false, fake) page to enter Instagram. At first glance, it will not differ from the standard in any way. Only one letter will be changed there, or some symbol invisible to the naked eye will be added. BUT it will be DIFFERENT. The user enters his username and password there and transfers it to a regular Instagram. Therefore, he will never guess that he was on this fake page. But ... but you will receive his nickname and password.
At first glance, it will not differ from the standard in any way. Only one letter will be changed there, or some symbol invisible to the naked eye will be added. BUT it will be DIFFERENT. The user enters his username and password there and transfers it to a regular Instagram. Therefore, he will never guess that he was on this fake page. But ... but you will receive his nickname and password.
You can read about how to create a phishing page on the Internet. We do not approve of this method and just brought it as really working and existing for those people who need to know how to hack the Instagram of a friend, girlfriend, wife, husband or their children through their computer.
How to hack someone else's Instagram? There are different ways. We told you about them. Now it's your turn - choose wisely. We certainly advise you to use our service. If difficulties arise, there are always online consultants on the site who will explain in detail and answer all your questions.