- Advertisement -
JOIN UGTECHMAG ON TELEGRAMThis guide is a complete step-by-step tutorial on how to hack an Instagram account and password.
- Advertisement -
Hacking an Instagram account does not happen automatically. You’ll need to read a lot of tricks and hacks before you find those that really work.
Either way, if you want to learn how to hack an Instagram account for free or monitor your kid’s social media accounts without them knowing, this article is for you.
To hack Instagram, Facebook (read this article for Facebook), or any WhatsApp account (read this article for WhatsApp), you need to be a little more patient. Many apps and websites make a fool out of people by promising them instant hacking of Instagram, which is ridiculous and not true.
It’s possible to penetrate Instagram security, but of course, with certain tricks & hacks. So this article will try to explain certain tricks & hacks which we tried out and hacked an Instagram account & password.
If you’re trying to hack Facebook or WhatsApp, then read the following
If you follow this article to the end, you’ll learn how to hack an Instagram account without writing a single line of code.
There is no other way of hacking Instagram automatically than the methods included in this guide.
Just know it takes patience and practice to become a hacker or hack someone’s Instagram.
Let’s get our hands dirty and dive into the tricks and hacks of hacking an Instagram account.
Contents
 3 Hack Instagram with Spyzie Applications
3 Hack Instagram with Spyzie Applications 1 Conclusion :
1 Conclusion :Before explaining to you the different methods of hacking Instagram accounts, I would like to present a very good software to decode all Instagram passwords simply from an email, a phone number, or a login ID.
Even if the account is protected by 2FA (double authentication) protection, PASS DECRYPTOR will be able to let you access the Instagram account without difficulty.
This software works on smartphones, tablets, and desktops.
Let’s hack a password easily now with PASS DECRYPTOR!
Keylogger Applications can be used to hack Instagram accounts and passwords using the keylogging feature. The Keylogging feature enables you to have access to keystrokes typed on the target device. This will help you to get hold of the target Instagram Password and username. They’re the most effective but may not be completely free.
They’re the most effective but may not be completely free.
Unfortunately, this application is not available free of charge (the reason it’s legit). To hack Instagram using MSPY, follow the step below. Mspy is a well-known spying application for hacking Instagram accounts.
Step 1: Go to mspy.com and purchase the application package of your choice.
Step 2: The Software will send you a confirmation email along with login details.
Step 3: View Mspy Demo to understand how the software works.
Step 4: Then install the application on the target device, and you’ll access it from your control panel.
Step 5: Access the Instagram features to view messages and pictures.
Step 6: Use the keylogging feature to monitor the Instagram account without the target’s knowledge. Once you get the target’s password, log in to Instagram on your computer with the target’s username and password.
Ikeymonitor records everything on the target device and sends you the results online. However, the keylogger application is not free of charge, though you can use the free version for three days. Follow the steps below to get started using ikeymonitor.
Step 1: Visit ikeymonitor.com & Select a free trial.
Step 2: Select device type, Yes I can get the device in my hand > and sign up with the required details as shown below.
Step 3: After signup, check your email account. You will receive a mail from ikeymonitor like this.
Step 4: Go back to ikeyMonitor window and log in. Wait for Dashboard to load. It will look like something below.
Step 5: Download and install ikeymonitor application on the target device using the window shown below. Follow steps according to your need.
Step 6: After downloading and installing the application on the target device, you can now receive logs online from your dashboard. You can also receive data from other applications as well.
You can also receive data from other applications as well.
Tip: If you want to only password then uninstall then install the Instagram app on your victim phone. It will log out the Instagram account ( or clear data app)
This is another application that will help you hack Instagram passwords without a lot of hustle. The application has got keylogger features that access keystrokes on the target device. Follow the steps below if you want to hack Instagram using Spayzie.
Step 1: Create an account with spyzie at my.spyzie.com
Step 2: You’ll receive a confirmation email with login details to your dashboard
Step 3: Install the application on the target device. Follow demo if you can’t install the application.
Step 4: Once installation is successful, login to spyzie dashboard using the login details provided in the email.
Step 5: Access the keylogger feature from the right menu of the dashboard. So wait for the target to access his/her Instagram, and you’ll receive a keylogger alert on your computers. You can use these detail to access target Instagram details from a PC.
The key-logger does its part of getting the target’s password for you. once you have the password, you can use it to access the target’s Instagram account on your computer and monitor his/her activities.
This method is going to show you how to hack Instagram account password of someone by only knowing your target username and without knowing how to code.
Here is a step-by-step guide on how to hack Instagram without Coding.
Step 1: Open Instagram Account: Tap the multicolored Instagram app icon. This will open your Instagram home page if you’re logged in.
This will open your Instagram home page if you’re logged in.
Step 2: Tap on Menu and select “Add Account “
Step 3: The login page of Instagram will open, enter the username of someone you want to hack, and since you don’t know their password, select Forgot Password.
Step 4: Verify it’s your account. Choose the SMS Option and enter your phone number.
Step 5: You’ll receive a password reset link in the form of an SMS to change the Instagram password.
Step 6: Open the SMS and click the link to reset the Instagram password from the Change Password section.
Step 7: Enter the new password of your choice and log in to the Instagram Account.
Congratulations, you have successfully hacked an Instagram account password.
Phishing is one of the most popular hacking tips and tricks online that will help you figure out someone’s Instagram password.
To hack Instagram account using phishing, you’ve to create a fake Instagram login page and send its link to a target user.
When the target logs in, the private login details are saved to a file, and the victim is redirected to the original Instagram page.
Below is an example of a phishing Instagram Login Page. If you want to tell it’s a fake page, just look at its URL. It’s not instagram.com.
How to hack Instagram using Phishing MethodThere are two ways you can hack an Instagram account using the phishing method:-
The first method is for geeks or programmers, and the other can be helpful to those who can’t write any line of code.
Method 1:
How to hack Instagram account with CodingCreating Instagram phishing site using free hostingThis method is very helpful if you have ever designed a website, or perhaps you’re a fast learner, if not use the 2nd method to crack the Instagram password.
In this method, you’re required to have some basic coding knowledge to help you create a phishing website.
Requirements of this method:-
Step 1: Create a website host (visit 5gbfree.com )
Step 2: Navigate to the Hosting plan and Select Free hosting. Sign Up with your details as required. (You’ll need to verify the email to continue)
Step 3: You’ll receive an email with login details after verification. ( Remember it may take a few hours for your account to be created )
Step 4: After Login, select the option “I will choose your free subdomain” and fill in the details as shown below.
Step 5:Create an Account, and you’ll be taken to a website dashboard.
Step 6: Verify your email address and open the account dashboard. Select the “Go to Cpanel” option next to your website name.
Select the “Go to Cpanel” option next to your website name.
Step 7: Go to ‘File Manager ‘, you’ll be automatically taken to the login page ( login with details from email ).
Sometimes it fails to login,To fix this, Go to “FTP Details” From your cpanel and change password . Try logging in again from the new password.
Step 8: After logging in, select “public_html ” and delete everything under it. Click Upload at the top bar.
Step 9: Download this Zip file, Extract it onto your PC, Upload it as shown below, and select the tick button.
Step 10: After a successful upload, you’ll see something like that below.
Congratulations, you have just created a successful phishing page to hack the Instagram Passwords of your target.
How to Check Hacked Instagram PasswordsTo check hacked Instagram accounts, Go to File Manager > password. html file. You’ll get the target usernames and passwords of those who used your phishing link.
html file. You’ll get the target usernames and passwords of those who used your phishing link.
That’s it. So just add /password.html after your phishing website, and you will see a list of your hacked accounts
Method 2 :
Create an Instagram Phishing page without coding or hostingIn this section, we shall use z-shadow.info to create an Instagram Phishing Page. Follow the steps below to see how this hack works.
Step 1: Create an account with z-shadow.info.
Step 2: After Logging in, Your account homepage will look like that below.
Step 3 : Scroll down and select page 3 > Number 35 ( Instagram ) > Click ‘ English ‘ > Press Ctrl+C (to copy the link )
Step 4: Open a new window and press Ctrl+V to paste the link in Url Tab.
How to Hack Instagram Usernames And PasswordsTo see the number of victims hacked, go back to your account homepage and refresh ‘ Total Victims ‘ under your account profile picture. Go to the top bar and Click My Victims Tab > Click to Continue.
Go to the top bar and Click My Victims Tab > Click to Continue.
Isn’t it fun and easy to hack Instagram’s password and account now?
How does it work?
Just copy the link from step 3 and send it as WhatsApp or SMS message to a target, persuading them to click. Congratulations, you must have hacked your first Instagram Account today.
Flexispy is another keylogger application that can be used to hack Instagram account passwords.
Like other Keylogger apps, the app is installed on the target device to monitor keystrokes on the device. Follow the procedure below to hack Instagram Account password with Flexispy.
Step 1: Install Flexispy application on target iPhone or Android device without them knowing.
Step 2: Login into portal.flexispy.com from your phone or computer and start monitoring activities of the target device
The Keylogger facility tracks every key punched by the iPhone user. You get a detailed report. In case he accesses Instagram, you get the notifications on your phone.
You are able to track the target’s keystrokes. Using this information, you can access his / her Instagram account.
Hack Instagram with ighackIghack is a secure Instagram hacker app that allows you to hack Instagram password-free.
The best part of the application is that it does not require any survey or download. It is available free on the internet.
In addition to being free to use, this app is compatible with every device. The application has a reputation for being authentic and untraceable.
Step 1: Visit ighack.net and click start hack
Step 2: Enter the target Instagram username and click next step.
Step 3: Allow the application to do the rest. The ighack server establishes contact with the Instagram server and searches for the password in the Instagram database by matching the username ID.
Step 4: On extraction of the data, the installed software program automatically decrypts the data.
Step 5: The system delivers the password to you and removes all traces of the activities done by the system. Hence, no one can track their way back.
This method is quite technical, however, if you follow the steps up to the bottom, you’ll be assured of getting positive results at least.
The method takes you through some quick steps to hack an Instagram account with python and brute force attack Kali Linux method.
To use this method, I recommend you first look through the requirements below and follow the step-by-step procedures as required.
Requirements for hacking Instagram using Brute Force method
You’ll need to have Kali Linux – the hacker’s OS on your computer to proceed. You can download Kali Linux from here and install it in less than an hour.
How does the Brute Force method work?
Brute Force method can hack Instagram by using a program that continuously inputs passwords into the target’s Instagram account. Sometimes it works some times it fails, remember it takes a lot of time so you have to be a bit patient if you want results.
Pro: It is easy to use, lots of beginners can use it
Con: It is a BruteForce attack, there is also a chance of failing
Step 1: Download this program https://github.com/Ethical-h5CK3R/Instagram.git from git repository as shown below to your computer.
Next, you’ll need to unzip the file, to do this open your command terminal and type in this command chmod -R 755 Instagram && cd Instagram
Step 2: Executing the program. To open the program, type the command ls to see what is inside the folder.
To open the program, type the command ls to see what is inside the folder.
Next, execute program instagram.py by typing this command in the terminal python instagram.py. You’ll get an error similar to that in the screenshot below.
This happens because we didn’t give the program the txt file, since this is a brute force method of hacking Instagram, we need to give the program a list of passwords that it can use.
Step 3: Get the password txt file. To do this, google ‘daniel miessler passwords github ‘ and select the first result. see screenshot below.
Under GitHub > Go to passwords > Choose one txt file with at least 10 million passwords, the bigger the better.
To save the file, copy the passwords into the text editor and save it as .txt in the Instagram folder which should be in the home directory.
Step 4: Time to hack your Instagram account. Open terminal and type command: cd Instagram.
Under the Instagram directory type: ls to see the files under it. Confirm that our txt file is there and continue with the procedure below. To execute program type :
python instagram.py Username Thetextfile.txt
At this step the Brute Force attack has started, it will say the attempts and what password it is currently trying. You’ll need to be patient enough before you’re successful.
If you get errors like Core.tor import TorManager, then install mechanize with: pip install mechanize, install requests with: pip install requests, install Tor with: sudo apt-get install tor
Hack Instagram using Social IQ Engineering SkillsIf you want to be a clever hacker, you’ve to be wise when getting along with all these Instagram hacks and tricks. For example, the way you share Instagram phishing site links shouldn’t be direct.
Use tricks such as getting a free recharge card on your phone by signing up at this link below. If you’ve a target who has an Instagram account linked to Facebook, you can hack a Facebook account using the same tricks and hacks.
Did you find this article helpful ? You can check the video above for more information .
This article is solely intended for education purposes, any misuse of the information shall not be the responsibility of the author nor Ugtechmag.com .
Graham CLULEY
July 15, 2019
Ad One product to protect all your devices, without slowing them down.
Free 90-day trial
A security researcher has been awarded $30,000 after discovering a serious vulnerability that could potentially have put any Instagram account at risk of being hacked.
Following a recent increase in rewards offered for the discovery of critical account takeover vulnerabilities in Facebook and Instagram, Indian security researcher Laxman Muthiyah chose to take a close look at the photo-sharing service.
As he describes in a blog post, Muthiyah explored whether there might be a vulnerability in how Instagram handled password reset requests for users who have forgotten their login credentials.
Mutiyah found that when users asked for a password reset via Instagram’s web interface, the site would email a reset link to the user’s email account.
After a few minutes of testing Mutiyah couldn’t find any bugs, and so turned his attention instead to how smartphone users recover access to their Instagram accounts.
What Mutiyah found was that Instagram offered the option for users locked out of their accounts to request that a six-digit secret security code be sent to their mobile phone number or email account. If that passcode is entered, a user can regain access to their Instagram account.
In theory, if a hacker could enter the six-digit security code they would be able to break into the Instagram account (and reset the password locking out the legitimate owner.)
Now, that passcode could potentially be stolen if a hacker had somehow managed to gain access to their target’s email account, or had hijacked control of their victim’s mobile phone number via a SIM swap scam. But Mutiyah wondered if there might be another way to break into accounts if neither of those options were available.
But Mutiyah wondered if there might be another way to break into accounts if neither of those options were available.
Mutiyah realised that all a hacker would need to do was enter the correct six digit code – a code that could be any combination between 000000 and 999999 – within the ten minute window Instagram would accept the code before expiring it.
Up to one million numbers to be entered within ten minutes, in order to change an Instagram account’s password.
Of course, the likes of Facebook and Instagram aren’t going to simply sit quietly as an automated script tries a brute force attack to guess the correct security code. Instead they have rate-limiting in place to detect when multiple attempts have been made to get past the security check and slow down subsequent attempts – meaning the ten minute window of opportunity expires.
In Mutiyah’s tests he discovered that when he cycled through 1000 attempts to guess an Instagram account’s security codes, 250 of them went through and the subsequent 750 requests were rate limited.
However, after a few days of testing the researcher was able to discover that Instagram’s rate limiting mechanism could be bypassed by rotating IP addresses (in other words, not using the same computer to brute force the recovery code) and sending concurrently from different IP addresses:
“Sending concurrent requests using multiple IPs allowed me to send a large number of requests without getting limited. The number of requests we can send is dependent on concurrency of reqs and the number of IPs we use. Also, I realized that the code expires in 10 minutes, it makes the attack even harder, therefore we need 1000s of IPs to perform the attack.”
Mutiyah says that he used 1000 different machines and IPs to achieve easy concurrency, and sent 200,000 requests in his tests. He shared a YouTube video with Facebook and Instagram’s security team to demonstrate the attack in action:
Of course, 200,000 requests isn’t quite the million requests that would be necessary to guarantee the correct recovery passcode would be entered to allow an Instagram account to be hijacked.
Mutiyah’s investigation concludes that in a real attack, 5000 IP addresses would be needed to hack an Instagram account. Although that sounds like a large number, it can actually be easily achieved at a low price (Mutiyah says there would be approximately US $150 cost if a cloud provider like Google or Amazon was used).
All Instagram users should be grateful that Laxman Muthiyah chose to responsibly disclose the security vulnerability to Instagram’s security team rather than monetize his discovery by selling it to online criminals.
It’s easy to imagine that a technique like this would be very attractive to many hackers interested in compromising Instagram accounts, and they might be prepared to pay much more than the $30,000 Muthiyah received in the form of a bug bounty.
All internet users are reminded to better secure their online accounts with strong, unique passwords and to enable two-factor authentication wherever possible.
A notification pops up on the smartphone screen: "We detected an unusual login attempt from Rio de Janeiro, Brazil.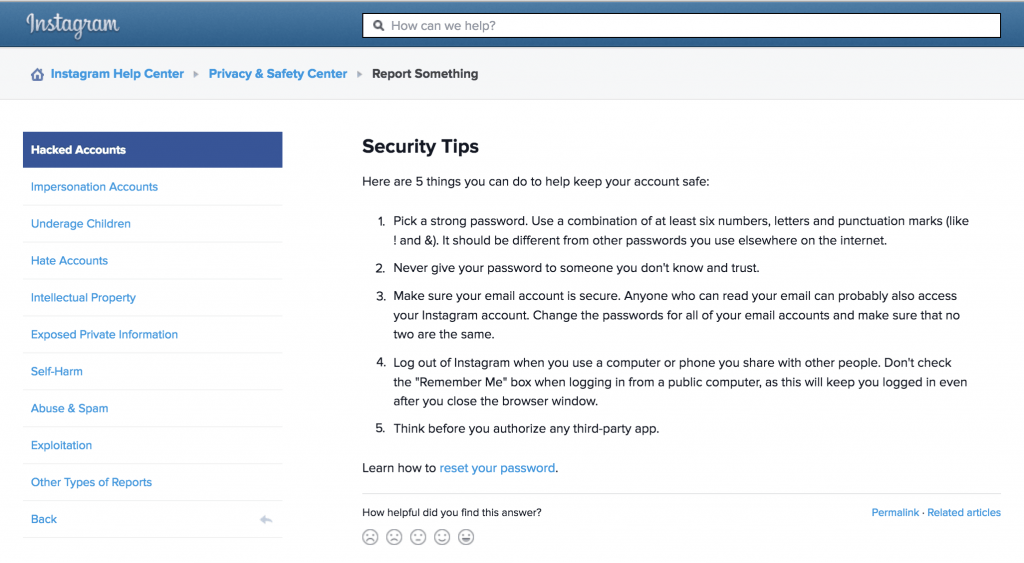 " The first reaction is panic, especially if you live in, say, Vladivostok. What could it be? System failure? Or is someone from the other side of the world really encroaching on your account?
" The first reaction is panic, especially if you live in, say, Vladivostok. What could it be? System failure? Or is someone from the other side of the world really encroaching on your account?
There is no way to panic in such a situation - this will only play into the hands of the burglars. So that you can remain calm and survive this incident with minimal losses, we will arm you with knowledge: we tell you what the matter might be and how to act. nine0003
First, let's figure out how a stranger could gain access to your account at all. There are several options here.
A third party site where you registered might have been leaked. Having acquired a list of logins, e-mail addresses and passwords, scammers use them for a substitution attack, that is, they try to enter stolen credentials on many sites. Unfortunately, many people set the same passwords to protect their accounts in different services - this is what criminals are counting on. nine0003
nine0003
Alternatively, your Facebook or Instagram credentials may have been leaked from the app you trusted them to. For example, in June last year, thousands of passwords from Instagram accounts leaked to the network, the owners of which used the Social Captain service to buy likes and followers. It turned out that he did not encrypt customer data, and anyone could get access to it. It is reasonable to assume that many users of the service have since experienced hacking attempts.
It may also be that some time ago you fell for phishing, and your login with a password fell into the hands of scammers directly. They clicked on some link, and on the page that opened, very similar to the Facebook or Instagram login screen, they entered their credentials. So they ended up with the criminal. For example, most recently, our experts discovered a phishing campaign in which victims were lured to phishing pages by the threat of blocking their Facebook account due to copyright infringement.
Your password may have been stolen by malware you picked up somewhere. Many Trojans have a built-in keylogger, a program that registers keystrokes on the keyboard. All logins and passwords that the victim enters, the keylogger directly passes into the hands of attackers.
Someone may have stolen your access token. So that you don't have to enter a password every time you log into Facebook or Instagram, it saves a small piece of information needed to log in to your computer, which is called a token or access token. If an attacker steals the current token, he will be able to log into the account without a username and password. nine0003
Tokens can be stolen in different ways. Sometimes this is done through vulnerabilities in Facebook itself - for example, in 2018, attackers were able to get access tokens to 50 million Facebook accounts. Also, attackers can use browser extensions to steal tokens.
It's possible that you logged into Facebook or Instagram from someone else's device - at a party, in an Internet cafe, in a hotel lobby, and so on - and did not log out after that. Or, for example, they forgot to log out of their account on a device that they had already sold or donated. Now someone has discovered your oversight and logged into your account. nine0003
Or, for example, they forgot to log out of their account on a device that they had already sold or donated. Now someone has discovered your oversight and logged into your account. nine0003
Your account may not have been hacked at all, but they are trying with a fake suspicious login notification. This is the same phishing that we talked about above, but a slightly different version of it. Instead of the threat of blocking, scammers can use fake suspicious login notifications with a link to phishing sites similar to the login page. Attackers expect that the victim in a panic will go to a fake site and enter their username and password there. nine0003
We have sorted out the possible causes, now it's time to act. To get started, log into your account - but in any case not through the link from the notification (as we already know, it can lead to a phishing site), but through the mobile application or by entering the address in the browser manually. If the password does not match and you can no longer log into your account, refer to the detailed instructions on what to do if your account has already been hijacked, which we published earlier.
If the password does not match and you can no longer log into your account, refer to the detailed instructions on what to do if your account has already been hijacked, which we published earlier.
If you are still allowed into your account, go to your account settings and verify the authenticity of the notification. For each social network, the path to the desired settings item will be different - see how this is done on Facebook and Instagram. Then go to the “Account Logins” section: if there are no suspicious entries there, then everything is in order, and the message about the hack was still phishing. nine0003
If you really see a suspicious one in the list of logins to your account, then it's time to hurry up to take protective measures - timely actions will help soften the blow:
 This will reset the access tokens.
This will reset the access tokens. Many famous break-ins began during the Christmas holidays. A few simple tips will reduce your risk of becoming the next victim.
A few simple tips will reduce your risk of becoming the next victim.
Avast solutions have a good reputation, but several incidents cast doubt on their reliability. We tell you whether you can trust Avast products.
How to watch the World Cup and not become a victim of fraud.
Take action on the website or app to secure your Instagram account if you think it has been hacked or is being used by someone else. If someone has accessed your account or you're having trouble signing in, visit this page in a browser on your computer or mobile device to help protect your account.
If someone has accessed your account or you're having trouble signing in, visit this page in a browser on your computer or mobile device to help protect your account.
You can also try to restore access according to the instructions below. Some of the actions listed are not available for all account types, but we recommend trying each one. nine0003
Check if you received an email from Instagram
If you received an email from [email protected] informing you that your email address has changed, please try to cancel and secure your account by clicking on the link. If some other information has changed (for example, the password), and you cannot restore the previous email address, request a login link or Instagram security code.
Request Instagram login link
To help us verify that the account belongs to you, request a login link, which we will send to your email address or phone number.
To request a login link:
Click Get help signing in (Android) or Forgot your password? (iPhone or browser).
Enter the username, email address, or phone number associated with your account and click Next. If you don't have access to that username, email address, or phone number, enter the login information you last used. Then click Can't reset your password? under the Next button and follow the instructions on the screen. nine0003
Pass verification to verify you are human (browser only).
Select your email address or phone number, and then click Next.
Follow the login link provided in the email or SMS and follow the instructions on the screen.
Request a security code or support on Instagram
If you are unable to recover your account using the login link, please request support.
To do this, follow the steps below. nine0003
Instagram app for Android
Instagram app for iPhone
Enter a secure email address that only you can access. After submitting your request, expect an email from Instagram with further instructions.
Learn more about what to do if you don't know your username.
Verify your identity
If you request support for an account that does not have a photo of you, you will receive an automatic email response from Meta Support. In order to verify your identity, we will ask you to provide the email address or phone number that you provided during registration, as well as the type of device from which you registered (for example, iPhone, Android device, iPad, etc.). nine0003
If you request support for an account that contains a photo of you, we will ask you to take a video selfie of you turning your head in different directions. This way we can verify that you are a real person and confirm your identity.
After sending a video selfie, you will receive an email from Instagram to the email address you provided. With the help of this video, we will be able to verify that you are a real person and verify your identity.
Note. The video you send will never appear on Instagram and will be deleted after 30 days.