by Nanah
Instagram is a social network that has been very successful since 2010. It is remarkable in the following areas: communication and chat, image distribution, social networks. Today, many teenagers are more present on Instagram than Facebook. Indeed, these young people consider that Facebook is more open and intrusive, yet they want to communicate discreetly on Instagram.
There are several valid reasons for hacking someone's Instagram account. It is more instructive to state from the outset that hacking into a personal account is illegal. This one is a violation of another's privacy. But, for more valid and acceptable reasons, here are some tips on how to hack an Instagram account.
First of all if you want to hack an instagram account via software:
Eyezy
Discreetly monitor Instagram accounts, posts. For private messages, look at Mspy (link further down the page).
Table des matières
As stated above, hacking an Instagram account is a violation of privacy. But, faced with inevitable contexts, an account can be hacked. Notably :
No matter the reason, there are always effective ways to access someone's Instagram account. However, we do not support illegal spying, especially without the consent of the targeted person.
Indeed, it is possible to hack an Instagram account without password. The most common problem is forgetting the password. Forgetting happens to everyone, how many times have you registered online without having physically noted down the password? Most users choose one general password for multiple accounts. However, this is the best way to get hacked. The hacker just gets it on one site and then tests it on every site he knows.
However, this is the best way to get hacked. The hacker just gets it on one site and then tests it on every site he knows.
In order to achieve your account hacking goal, you need to use compatible software. Here's how:
Indeed, this technique worked very well until others arrived on the market:
These new methods have reduced the effectiveness of the brute force method.
In other words, and if not used, hacking an Instagram account is illegal and considered a crime. We strongly advise against any use of hacks for malicious purposes.
Answer to the question, is it possible to hack an Instagram account without having the password?
Currently it is impossible to hack an Instagram account without the methods above and without having installed the software that I have put at the top or bottom of this page.
I advise you to stop your research because other sites want you to install viruses! Some sites will offer you to download software but to hack your computer. If there is a way to hack your Instagram account or another, we will tell you on this page. So you can put it in favorites but it will be impossible or almost.
For parents, couples or people who are close, and you want to be able to monitor and spy on the Instagram account and everything your child, spouse, boyfriend or other does
There is currently only one tool that I advise you to test
See someone's private messages on Instagram
It's a tool that's perfect for seeing someone's messages without them knowing, so go try it out!
For those who have lost their account and want to recover it, you should know that the tool just above allows you to do everything remotely on your phone, so even for yourself, I recommend that you install it on your phone (myself, I have it in case someone steals my phone or my Instagram account!)
Otherwise to recover your account the only way is to make requests to the support, to try to find your password. Unfortunately there is no other solution :(. Beware of other sites that want to scam you by calling phone numbers. This will cost you 20$ per week for no results.
Unfortunately there is no other solution :(. Beware of other sites that want to scam you by calling phone numbers. This will cost you 20$ per week for no results.
Another page on our site to help you on your social network:
When I’m not studying videos of raccoons online (know your enemy!), I’m fielding requests from wannabe hackers all around the world because I work for Hacker Highschool. So, wannabe hackers tend to think our curriculum is there as a checklist of scriptkiddie tools that lets them DoS your online competition of Banjo Hero or creep into private Instagram accounts.
And it is. But it isn’t.
First, I recognize that hacking an Instagram password is wrong. I get it. Even if it’s their brother’s Instagram account they want to get into. Because it’s family that makes it okay, I guess. So yes, it's illegal, but being illegal doesn't make it wrong. But it’s wrong because guessing a password isn’t hacking, and not because it’s their brother. And this is why so many nascent hacker-wannabes who want to learn hacking don’t really want to learn hacking. They want to learn computer magic, and it doesn’t really work like that.
How it works is actual work. And it’s a grind sometimes. What’s strange is that so many people today can spend actual days virtually cutting virtual trees in a virtual world to get to level three tree warrior, but won’t spend an hour trying requests through Tamper Data to understand how Instagram on the web is authenticating people differently than the app. Strange because both are really not much more than pushing a cursor around a screen.
So, teaching you hacking is partly about teaching you how to set up and execute a kind of work grind. Then there’s the mindset thing too. But you know what, you need a mindset to get out of bed and go to work too, and that trumps the hacker mindset in the mornings. So, let’s leave the hacker mindset for those who already have the will to do the work grind mindset, because you won’t have one without the other.
The last part of teaching you to hack an Instagram account is that by the time I teach you what you need to know with OS, protocols, services, daemons, applications, authentication, and encryption, and what you need to do with hiding, relaying, bouncing, testing, fuzzing, tracing, trying, retrying, and learning from your frequent failures, you’ll know too much about how little you really know and how you could get caught doing it. So, you probably won’t be doing anything illegal. They say a little knowledge is a dangerous thing, but when we’re talking about a skill like hacking that focuses on knowledge-gettin’ then you can expect to quickly have more than enough knowledge to see your own foolishness.
Unless you want me to just tell you to use the instacrack tool for Windows available on the ISECOM website to just put in an account name and view private account pictures. But that’s telling, not teaching, and it’s running a tool and not hacking. Also, don’t ask me how to cook if you want me to show you how to warm up a TV dinner.
But if that’s really what you want, then you never wanted to be a hacker, which means your life is about only having enough knowledge to be dangerous. Which is okay if you want to be an amateur assassin or a cashier in a natural foods store for the rest of your life. Not judging. We all have our dreams. But then you’re looking in the wrong place.
Next thing to understand: hacking isn't a tool, it's a methodology. You likely won't be able to hack an established service without considerable time spent learning its operations and interactions. Which isn’t necessarily hard. It’s actually pretty straight-forward.
The fact of this is that there's only two ways to steal anything: either you take it, or someone gives it to you.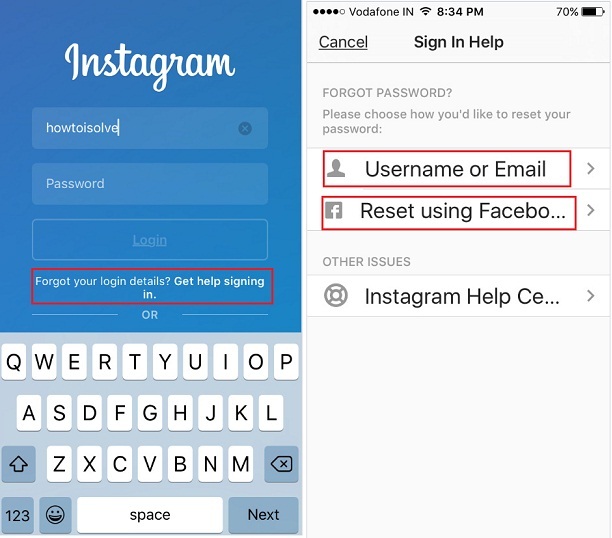 You need to trick Instagram to give you their credentials. Or you need to trick the person whose credentials you want to steal into giving it to you. Or you need to take it from them, or Instagram. But it's likely you won't be able to take it from Instagram. Not impossible, just not likely because they have a lot more people with a lot more experience working on securing it then you have for breaking it. Supposedly. Who knows? Maybe you’ll get lucky. People win the lottery all the time. That’s why so many people play it.
You need to trick Instagram to give you their credentials. Or you need to trick the person whose credentials you want to steal into giving it to you. Or you need to take it from them, or Instagram. But it's likely you won't be able to take it from Instagram. Not impossible, just not likely because they have a lot more people with a lot more experience working on securing it then you have for breaking it. Supposedly. Who knows? Maybe you’ll get lucky. People win the lottery all the time. That’s why so many people play it.
Then those two ways actually expand into four tactics that you try against both the target sender and target receiver. These four:
 ). As any family will tell you, from bath tubs to babies, everything leaks. It’s the same with computers. The Internet exists because protocols play nice, communicate, and share, or else you’d never get online and go anywhere. So, ask and find out what’s sharing what. And the better you listen, the more you know.
). As any family will tell you, from bath tubs to babies, everything leaks. It’s the same with computers. The Internet exists because protocols play nice, communicate, and share, or else you’d never get online and go anywhere. So, ask and find out what’s sharing what. And the better you listen, the more you know. ). Do the thing the designers didn’t anticipate to ever happen and you’ll force the system into doing something insecure.
). Do the thing the designers didn’t anticipate to ever happen and you’ll force the system into doing something insecure.So there. Use those four. Now you know where your targets are and the tactics to try. That leaves you with a few options in your grind. If you need more specific examples on you how you would apply these four tactics to real-world, how would you take over your brother’s Instagram account, here's five common ones to get you started:
 Since you control the device you can control the environment and capture anything typed into it.
Since you control the device you can control the environment and capture anything typed into it.Now I’d like to tell you don’t do things that have worked before because system designers learn from their mistakes and the mistakes made by others. Unfortunately, they don’t. It’s not like Engineering students are forced to take a competency exam in all the mistakes previously done in engineering. Oh, if only! I would totally take that class just for fun! But they don’t, so feel free to try things that worked in the past.
Unfortunately, they don’t. It’s not like Engineering students are forced to take a competency exam in all the mistakes previously done in engineering. Oh, if only! I would totally take that class just for fun! But they don’t, so feel free to try things that worked in the past.
So that's it. No matter what you do, it will require more than just a tool. Because if was a tool that does some magic and then you get in, then you probably can’t afford that tool. Good magic isn’t cheap. Think about it: anyone who went through all the hard work to figure out how to do that wouldn't release a tool, as that info is way too profitable.
So, there’s no Windows-based instacrack tool either. Just kidding! I’m sure you already checked though.
A notification pops up on the smartphone screen: "We detected an unusual login attempt from Rio de Janeiro, Brazil." The first reaction is panic, especially if you live in, say, Vladivostok.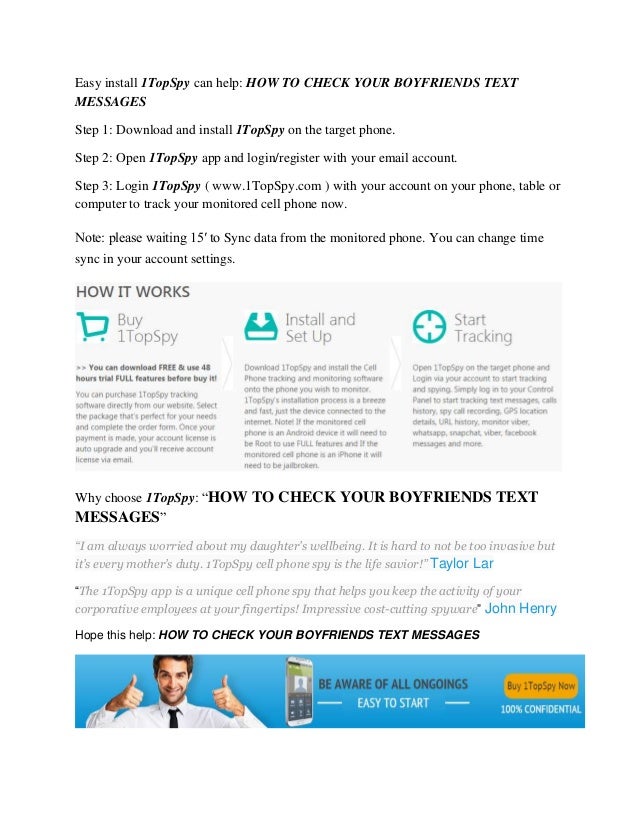 What could it be? System failure? Or is someone from the other side of the world really encroaching on your account?
What could it be? System failure? Or is someone from the other side of the world really encroaching on your account?
There is no way to panic in such a situation - this will only play into the hands of the burglars. So that you can remain calm and survive this incident with minimal losses, we will arm you with knowledge: we tell you what the matter might be and how to act. nine0003
First, let's figure out how a stranger could gain access to your account at all. There are several options here.
A third party site where you registered might have been leaked. Having acquired a list of logins, e-mail addresses and passwords, scammers use them for a substitution attack, that is, they try to enter stolen credentials on many sites. Unfortunately, many people set the same passwords to protect their accounts in different services - this is what criminals are counting on. nine0003
Alternatively, your Facebook or Instagram credentials may have been leaked from the app you trusted them to. For example, in June last year, thousands of passwords from Instagram accounts leaked to the network, the owners of which used the Social Captain service to buy likes and followers. It turned out that he did not encrypt customer data, and anyone could get access to it. It is reasonable to assume that many users of the service have since experienced hacking attempts.
For example, in June last year, thousands of passwords from Instagram accounts leaked to the network, the owners of which used the Social Captain service to buy likes and followers. It turned out that he did not encrypt customer data, and anyone could get access to it. It is reasonable to assume that many users of the service have since experienced hacking attempts.
It may also be that some time ago you fell for phishing, and your login with a password fell into the hands of scammers directly. They clicked on some link, and on the page that opened, very similar to the Facebook or Instagram login screen, they entered their credentials. So they ended up with the criminal. For example, most recently, our experts discovered a phishing campaign in which victims were lured to phishing pages by the threat of blocking their Facebook account due to copyright infringement.
Your password may have been stolen by malware you picked up somewhere. Many Trojans have a built-in keylogger, a program that registers keystrokes on the keyboard. All logins and passwords that the victim enters, the keylogger directly passes into the hands of attackers.
Many Trojans have a built-in keylogger, a program that registers keystrokes on the keyboard. All logins and passwords that the victim enters, the keylogger directly passes into the hands of attackers.
Someone may have stolen your access token. So that you don't have to enter a password every time you log into Facebook or Instagram, it saves a small piece of information needed to log in to your computer, which is called a token or access token. If an attacker steals the current token, he will be able to log into the account without a username and password. nine0003
Tokens can be stolen in different ways. Sometimes this is done through vulnerabilities in Facebook itself - for example, in 2018, attackers were able to get access tokens to 50 million Facebook accounts. Also, attackers can use browser extensions to steal tokens.
It's possible that you logged into Facebook or Instagram from someone else's device - at a party, in an Internet cafe, in a hotel lobby, and so on - and did not log out after that. Or, for example, they forgot to log out of their account on a device that they had already sold or donated. Now someone has discovered your oversight and logged into your account. nine0003
Or, for example, they forgot to log out of their account on a device that they had already sold or donated. Now someone has discovered your oversight and logged into your account. nine0003
Your account may not have been hacked at all, but they are trying with a fake suspicious login notification. This is the same phishing that we talked about above, but a slightly different version of it. Instead of the threat of blocking, scammers can use fake suspicious login notifications with a link to phishing sites similar to the login page. Attackers expect that the victim in a panic will go to a fake site and enter their username and password there. nine0003
We have sorted out the possible causes, now it's time to act. To get started, log into your account - but in any case not through the link from the notification (as we already know, it can lead to a phishing site), but through the mobile application or by entering the address in the browser manually. If the password does not match and you can no longer log into your account, refer to the detailed instructions on what to do if your account has already been hijacked, which we published earlier.
If the password does not match and you can no longer log into your account, refer to the detailed instructions on what to do if your account has already been hijacked, which we published earlier.
If you are still allowed into your account, go to your account settings and verify the authenticity of the notification. For each social network, the path to the desired settings item will be different - see how this is done on Facebook and Instagram. Then go to the “Account Logins” section: if there are no suspicious entries there, then everything is in order, and the message about the hack was still phishing. nine0003
If you really see a suspicious one in the list of logins to your account, then it's time to hurry up to take protective measures - timely actions will help soften the blow:
 This will reset the access tokens.
This will reset the access tokens. Many famous break-ins began during the Christmas holidays. A few simple tips will reduce your risk of becoming the next victim.
A few simple tips will reduce your risk of becoming the next victim.
Avast solutions have a good reputation, but several incidents cast doubt on their reliability. We tell you whether you can trust Avast products.
How to watch the World Cup and not become a victim of fraud.
Take action on the website or app to secure your Instagram account if you think it has been hacked or is being used by someone else. If someone has accessed your account or you're having trouble signing in, visit this page in a browser on your computer or mobile device to help protect your account.
If someone has accessed your account or you're having trouble signing in, visit this page in a browser on your computer or mobile device to help protect your account.
You can also try to restore access according to the instructions below. Some of the actions listed are not available for all account types, but we recommend trying each one. nine0003
Check if you received an email from Instagram
If you received an email from [email protected] informing you that your email address has changed, please try to cancel and secure your account by clicking on the link. If some other information has changed (for example, the password), and you cannot restore the previous email address, request a login link or Instagram security code.
Request Instagram login link
To help us verify that the account belongs to you, request a login link, which we will send to your email address or phone number.
To request a login link:
Click Get help signing in (Android) or Forgot your password? (iPhone or browser).
Enter the username, email address, or phone number associated with your account and click Next. If you don't have access to that username, email address, or phone number, enter the login information you last used. Then click Can't reset your password? under the Next button and follow the instructions on the screen. nine0003
Pass verification to verify you are human (browser only).
Select your email address or phone number, and then click Next.
Follow the login link provided in the email or SMS and follow the instructions on the screen.
Request a security code or support on Instagram
If you are unable to recover your account using the login link, please request support.
To do this, follow the steps below. nine0003
Instagram app for Android
Instagram app for iPhone
Enter a secure email address that only you can access. After submitting your request, expect an email from Instagram with further instructions.
Learn more about what to do if you don't know your username.
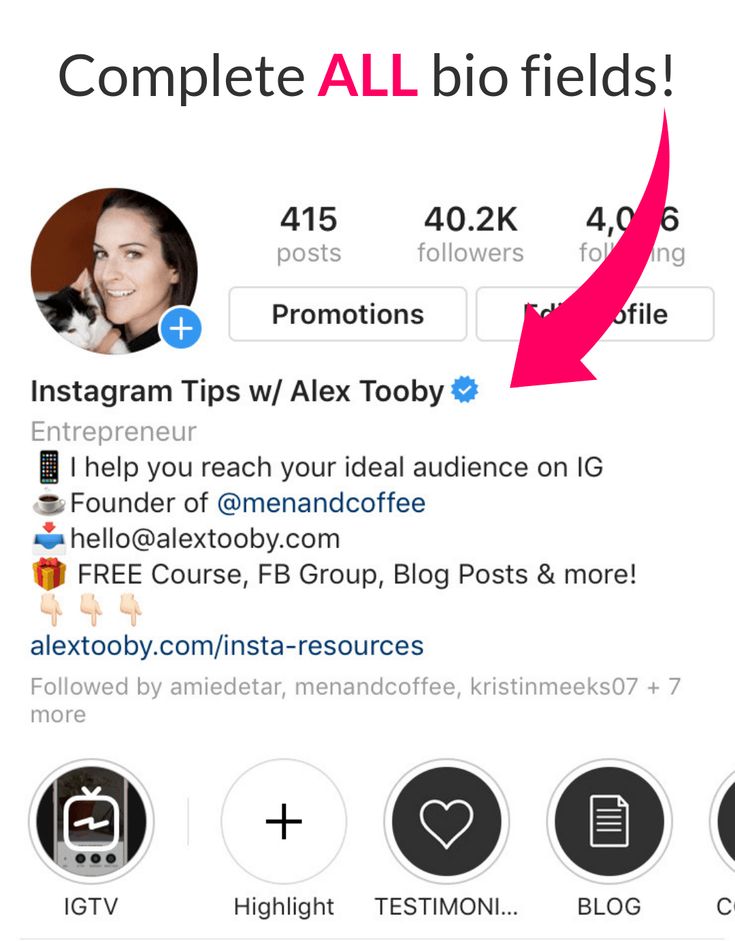
Verify your identity
If you request support for an account that does not have a photo of you, you will receive an automatic email response from Meta Support. In order to verify your identity, we will ask you to provide the email address or phone number that you provided during registration, as well as the type of device from which you registered (for example, iPhone, Android device, iPad, etc.). nine0003
If you request support for an account that contains a photo of you, we will ask you to take a video selfie of you turning your head in different directions. This way we can verify that you are a real person and confirm your identity.
After sending a video selfie, you will receive an email from Instagram to the email address you provided. With the help of this video, we will be able to verify that you are a real person and verify your identity.
Note. The video you send will never appear on Instagram and will be deleted after 30 days.